In the increasingly complex landscape of digital marketing, the adage "content is king" often overshadows a more fundamental truth: "audience validity is sovereign." While marketers pour resources into crafting compelling narratives, engaging visuals, and sophisticated AI-driven personalization, a critical prerequisite is often relegated to a mere maintenance task: email verification. This oversight, known as the "downstream fallacy," can transform meticulously planned campaigns into costly endeavors, eroding return on investment (ROI), damaging sender reputation, and fostering internal friction. Email verification is not merely a technical checkbox; it is the bedrock upon which all successful digital outreach is built, ensuring that every message reaches a genuine, engaged recipient and maximizing the impact of marketing spend.
The Foundation of Digital Outreach: Why Email Verification is Non-Negotiable
Email marketing remains one of the most powerful and cost-effective channels for customer engagement and acquisition, boasting an average ROI of $36 for every $1 spent, according to recent studies by Litmus and Campaign Monitor. However, this impressive figure is contingent on one crucial factor: deliverability. Without robust email verification, even the most exquisitely designed email with perfectly targeted messaging risks falling into the digital void of an invalid or nonexistent address. This isn’t just a minor inefficiency; it’s a systemic vulnerability that puts an invisible ceiling on campaign performance.
The immediate consequence of sending emails to invalid addresses is a heightened bounce rate. Email bounces are categorized into "soft bounces" (temporary issues like a full inbox or server downtime) and "hard bounces" (permanent failures due to nonexistent addresses or invalid domains). While soft bounces are generally recoverable, a high volume of hard bounces signals to mailbox providers (like Gmail, Outlook, Yahoo) that a sender’s data management practices are subpar. This negative signal directly impacts sender reputation, a crucial metric that determines whether future emails land in the inbox, the spam folder, or are blocked entirely. Industry data suggests that a bounce rate exceeding 2% can begin to negatively affect sender reputation, with anything above 5% being a serious red flag.
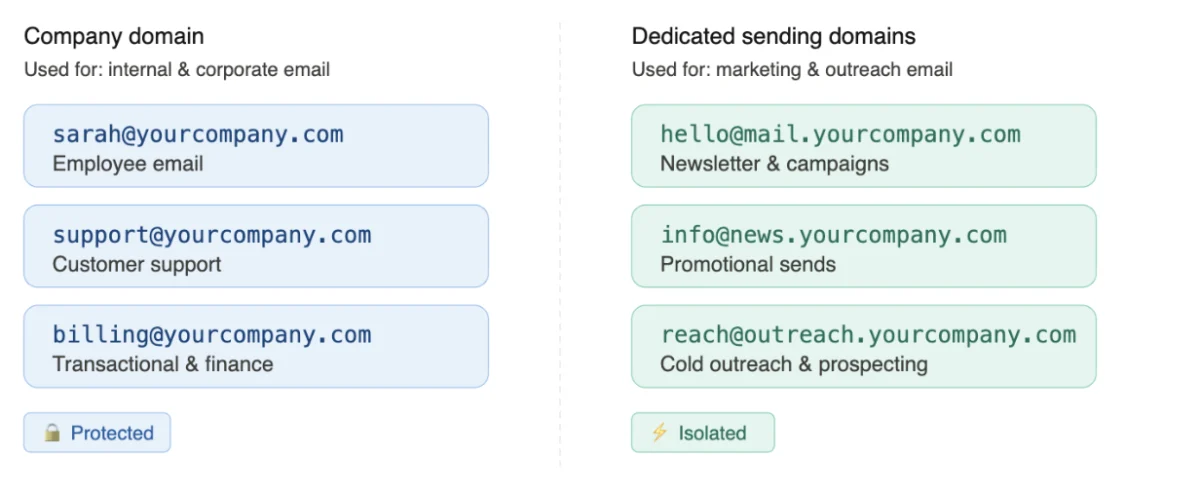
The ramifications of a damaged sender reputation extend far beyond a single campaign. Once an IP address or domain is flagged, subsequent emails, even those sent to legitimate leads, face an uphill battle for inbox placement. This can lead to a vicious cycle: poor deliverability reduces engagement, further harming reputation, and ultimately diminishing the effectiveness of an entire email program. Proactive verification, therefore, acts as a critical risk management strategy, empowering marketers to scale their campaigns confidently without the constant fear of suspension or diminished reach. It cleans the email database, establishing a sound foundation of valid data that allows creative assets to be fully leveraged, ensuring that efforts are not wasted and that relevant leads actually see the emails intended for them.
Addressing the "Downstream Fallacy": Prioritizing Data Quality Upstream
A common pitfall in marketing departments is the "downstream fallacy," where disproportionate resources are allocated to the latter stages of the marketing workflow – such as content creation, A/B testing, and campaign execution – while neglecting the foundational quality of the data from the outset. This creates a scenario where sophisticated efforts are built upon shaky ground. Marketers often face immense pressure to demonstrate visible results through email output, yet the true success of these endeavors becomes impossible to accurately gauge if the underlying email list is riddled with invalid addresses.

The contemporary email marketing landscape is increasingly characterized by advancements in artificial intelligence (AI) and hyper-personalization. AI tools are being deployed to generate copy, optimize send times, and predict customer behavior, while hyper-personalization aims to deliver bespoke experiences to individual recipients. However, the efficacy of even the most innovative AI algorithms or granular personalization strategies is severely compromised if the emails are being sent to non-existent recipients. Sending a perfectly crafted, AI-generated, hyper-personalized email to an invalid address is the digital equivalent of shouting into an empty room – a complete waste of time, effort, and technological investment.
Beyond the technological inefficiencies, the downstream fallacy exacerbates a prevalent issue: the misalignment between marketing and sales teams. Marketing’s primary objective is to generate qualified leads for sales. When marketing passes on leads that include invalid email addresses, sales teams waste valuable time and resources attempting to contact "ghosts." This not only diminishes sales productivity but also erodes trust between the two departments, fostering internal friction and hindering overall business growth. A robust email verification process ensures that the leads marketing provides to sales are genuinely valid, fostering greater collaboration and efficiency across the sales funnel.
Compounding these challenges are tightening marketing budgets. A 2025 Gartner report highlighted that marketing budgets have flatlined at 7.7 percent of overall company revenue, underscoring the imperative for maximum efficiency. In such an environment, every dollar spent must yield demonstrable results. Sending emails to invalid domains or non-existent contacts is a direct waste of budget, as email service providers (ESPs) typically charge based on subscriber count or email volume. Correcting the downstream fallacy necessitates a cultural shift, placing greater emphasis on upstream data quality and treating audience validity as the indispensable launchpad for all subsequent marketing activities.
The Hierarchy of Email Marketing Success: A Paradigm Shift
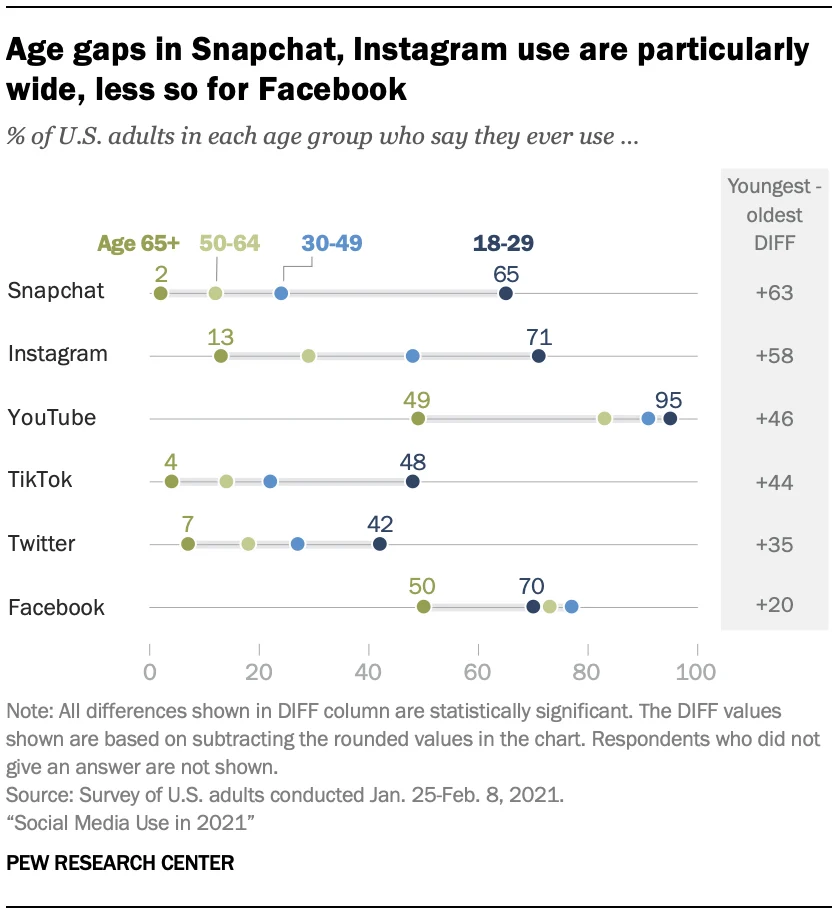
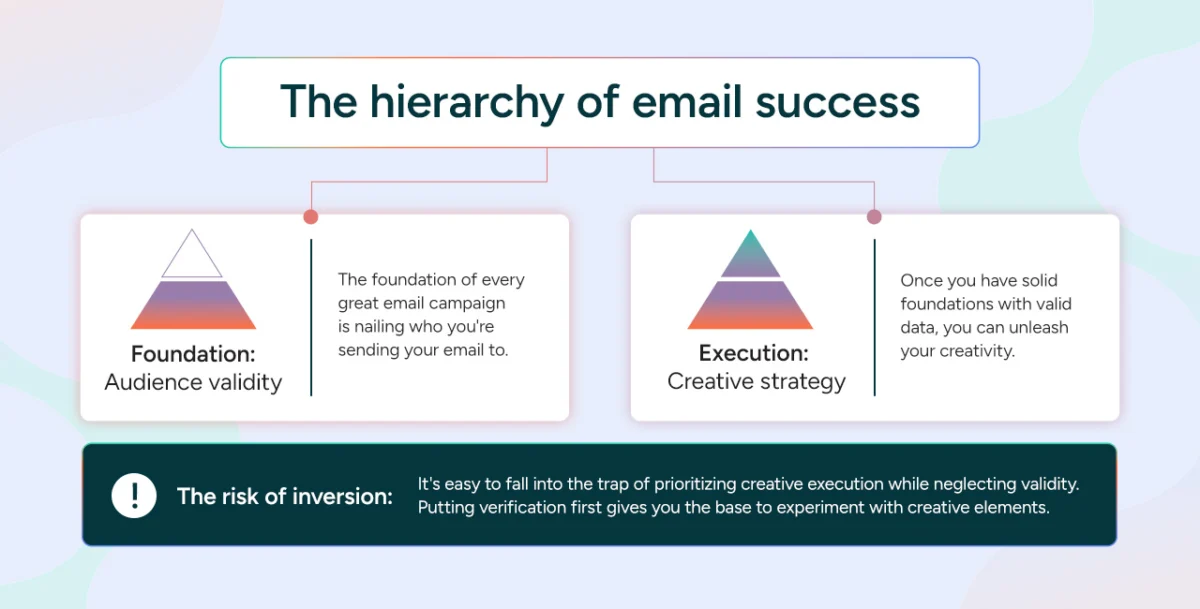
Achieving email marketing success is akin to constructing a sturdy building; it requires a specific, logical sequence of steps, where each layer builds upon a solid foundation. The "Hierarchy of Email Success" redefines traditional priorities, asserting that audience validity must precede creative execution.
-
Foundation: Audience Validity
The absolute bedrock of any effective email campaign is a meticulously validated audience. This foundational layer involves accurately identifying who the emails are being sent to, ensuring that each address corresponds to an active, legitimate recipient. This step is crucial not only from a technical deliverability standpoint but also from a strategic messaging perspective, preventing marketers from "shouting into the void." By establishing good data foundations, organizations ensure that their resources—both creative and financial—are utilized to their fullest potential. This initial step is vital for immediate campaign performance and crucial for long-term scalability, guaranteeing that as lists grow, bounce rates remain low and sender reputation stays intact. -
Execution: Creative Strategy
Only once a solid foundation of valid data is established can marketers truly unleash their creativity. This layer encompasses all aspects of email design, compelling copy, sophisticated personalization tactics, and A/B testing. While creative elements are directly responsible for capturing attention, driving engagement, and prompting conversions, their effectiveness is entirely dependent on the deliverability achieved through robust email verification. A brilliantly conceived campaign is rendered moot if it never reaches the intended inbox. -
The Risk of Inversion
A prevalent and dangerous trap is the inversion of this hierarchy—prioritizing creative execution over the fundamental health and validity of the email list. This can create a false sense of security, where impressive metrics on open rates or click-through rates are reported, but the underlying problem of low deliverability due to a bloated, unverified list remains unaddressed. Correcting this inversion requires a significant cultural shift within marketing teams, championing clean data metrics (like low bounce rates and high deliverability) with the same fervor typically reserved for engagement metrics (like click-through rates and conversions). As one marketing director, Sarah Chen, recently stated, "We used to chase open rates, but now we understand that ensuring our emails even reach the inbox is the real first battle. Without clean data, every other metric is just a delusion." This shift fosters a more data-driven, accountable, and ultimately more successful marketing operation.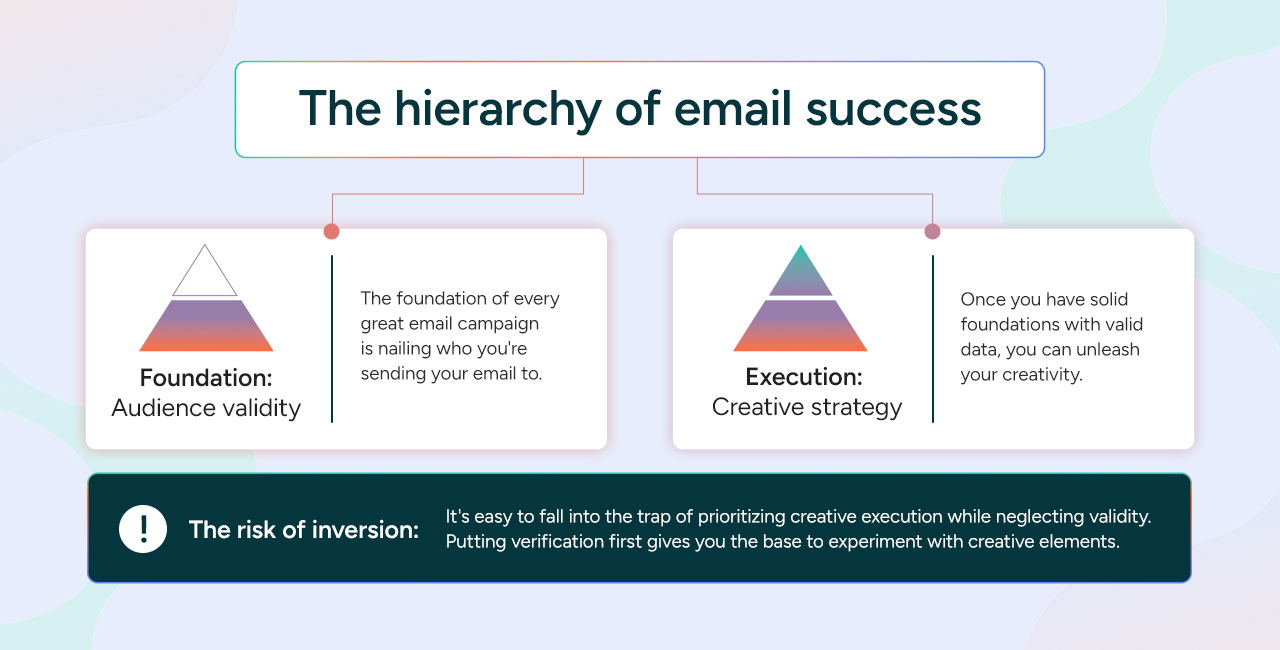
Unpacking the Mechanics: Beyond Basic Syntax Checks
The technical process of email verification extends far beyond a simple check for an "@" symbol. Modern verification tools employ a sophisticated multi-stage process to ascertain the validity and deliverability of an email address:
- Syntax Validation: The initial step involves checking if the email address adheres to standard formatting rules (e.g.,
[email protected]). This weeds out obvious typos and malformed addresses. - Domain Validation (DNS & MX Records): The tool verifies that the domain name (e.g.,
domain.com) exists and has valid Mail Exchange (MX) records, which specify the mail servers responsible for accepting email for that domain. If no MX records exist, the domain cannot receive mail. - SMTP Connection & User Verification: This is the most crucial step. The verification tool attempts to establish an SMTP (Simple Mail Transfer Protocol) connection with the domain’s mail server, simulating a send attempt. During this process, it can often determine if the mailbox for the specific user (e.g.,
user) exists and is active without actually sending an email. - Disposable Email Detection: Identifies addresses from temporary email services (e.g.,
mailinator.com), which are often used for one-time sign-ups and yield no long-term value. - Role-Based Email Detection: Flags generic addresses like
info@,sales@, oradmin@. While valid, these may not be ideal for personalized marketing and can sometimes indicate lower engagement. - Spam Trap Identification: Utilizes databases of known spam traps (email addresses specifically designed to catch spammers) to identify and remove them from lists, preventing severe damage to sender reputation.
- Greylisting Detection: Identifies mail servers that temporarily reject emails from unknown senders as a spam prevention technique.
- Temporary Issues vs. Permanent Failures: A key capability is distinguishing between temporary delivery issues (e.g., full mailbox, server timeout) and permanent failures (nonexistent user, invalid domain). This allows marketers to prune their lists effectively, removing hard bounces while potentially segmenting soft bounces for re-engagement attempts.
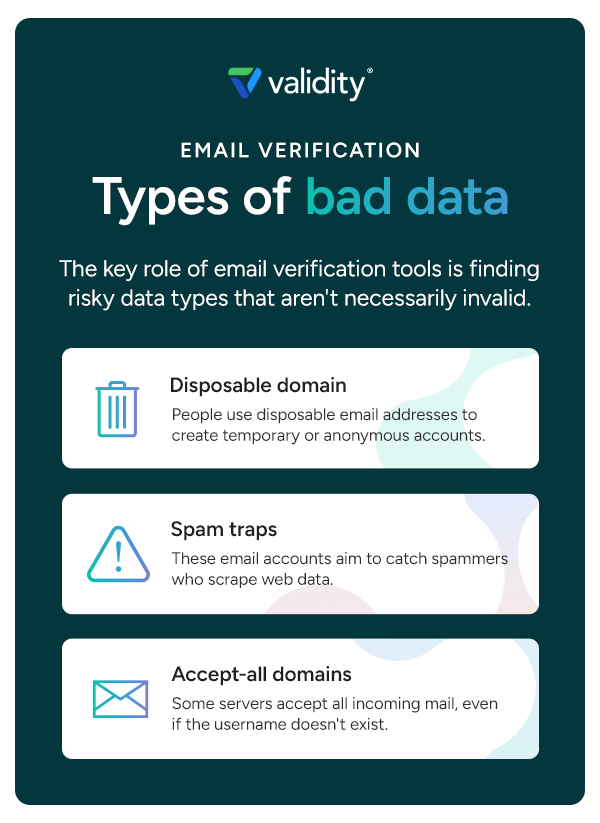
Types of Bad Data
A robust email verification tool is essential for identifying and mitigating various types of risky data that can undermine marketing efforts:
- Non-existent Email Addresses: The most common form of bad data, leading to hard bounces and sender reputation damage.
- Disposable Email Addresses: Often used to avoid spam or protect privacy, these accounts are temporary and offer no long-term value for marketing.
- Spam Traps (Honeypots): These are email addresses designed to catch spammers. Hitting a spam trap can severely blacklist a sender’s IP and domain, leading to widespread deliverability issues. They can be pristine (never used for anything legitimate) or recycled (old, inactive addresses repurposed as traps).
- Typographical Errors: Simple human mistakes during data entry, often correctable at the point of capture.
- Role-Based Emails: While valid, addresses like
support@ornoreply@are less effective for personalized outreach and can skew engagement metrics. - High-Risk Domains: Domains associated with known spam activities, malicious software, or purchased email lists that often contain invalid or low-quality contacts.
- Inactive/Dormant Accounts: While initially valid, these accounts become inactive over time, contributing to low engagement and potentially being converted into recycled spam traps.
Beyond technical performance, email verification provides a crucial first line of defense for regulatory compliance. By identifying and removing spam traps or high-risk domains associated with purchased lists or poor data hygiene, marketers significantly minimize their risk of violating stringent data protection regulations such as the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and Canada’s Anti-Spam Legislation (CASL). These regulations mandate consent for communication and proper data management, making proactive verification an indispensable tool for legal adherence.
The Real Cost of Bad Data: Tangible and Intangible Impacts
Eliminating bad data from email lists isn’t merely about boosting technical performance; it’s a direct safeguard for an organization’s bottom line, impacting both direct and indirect costs, as well as significant opportunity costs.
Direct Costs:
Email Service Providers (ESPs) typically charge clients based on the volume of emails sent or the number of active subscribers on their list. A bloated list containing invalid or non-existent contacts translates directly into wasted expenditure. By regularly purging these unproductive entries, organizations can often reduce their subscriber count, potentially moving down to a lower pricing tier with their ESP, leading to immediate and tangible cost savings. This ensures that every dollar spent on email infrastructure and sending capacity is directed towards verifiable, reachable leads.
Indirect Costs:
The ripple effects of bad data extend far beyond direct financial outlays:
- Skewed Analytics and Impaired Optimization: Bad data fundamentally distorts marketing analytics. If a significant portion of emails never reach their destination, open rates, click-through rates, and conversion rates become unreliable. This makes accurate A/B testing impossible and leads to flawed strategic decisions. Without a verified email list, marketers operate on educated guesses rather than precise insights, hindering their ability to optimize future strategies and confidently report on marketing’s true impact on the business.
- Damaged Sender Reputation and Deliverability: Every hard bounce caused by an invalid address chips away at a sender’s domain reputation. Over time, this cumulative damage leads to mailbox providers increasingly deprioritizing emails from that domain, marking them as spam, or blocking them entirely. The indirect cost here is a significant loss of potential customer engagement and revenue, as future campaigns struggle to reach the inbox. Rebuilding a damaged sender reputation is a lengthy and arduous process, requiring substantial time and resources. Proactive verification ensures a high-quality list, minimizing bounces and protecting this invaluable asset.
- Operational Drag and Inter-Departmental Friction: When marketing passes invalid leads to sales, it creates significant operational inefficiencies. Sales teams waste valuable time chasing contacts that don’t exist, leading to frustration, reduced productivity, and a tangible loss of trust in the quality of marketing-generated leads. This breakdown in inter-departmental synergy can have broader negative impacts on company culture and overall revenue attainment. Regular verification equips sales teams with reliable leads, allowing them to focus on genuine opportunities and increase their impact.
- Technical Overhead and Storage Costs: Bloated databases, filled with invalid or outdated information, can significantly slow down sync times between various marketing automation platforms, CRM systems, and other business applications. This unnecessary data load increases storage costs for backups and maintenance, adding another layer of indirect expenditure. Regular list hygiene reduces this technical burden, streamlining operations.
Opportunity Costs:
Perhaps the most insidious cost is the opportunity cost – the potential value lost from leads that could have been salvaged or acquired more efficiently. This includes email addresses that contained simple human typos (e.g., gamil.com instead of gmail.com) which could have been corrected at the point of capture. Real-time verification, by prompting users to correct errors instantly, creates a frictionless user experience. This not only reinforces the brand’s professionalism but also ensures that prospects immediately receive the information they requested, preventing lead loss and capturing potential revenue. Each unverified, incorrect email represents a missed opportunity for engagement, conversion, and long-term customer value.
Implementing a Robust Email Verification Strategy: A Multi-pronged Approach
Effective email verification is not a one-time event but a continuous process integrated into the marketing workflow. A comprehensive strategy involves several key types of verification:
-
Real-time Verification:
This is the most proactive form of verification, implemented at the point of data collection (e.g., on web forms, signup pages). Real-time tools leverage Application Programming Interfaces (APIs) to instantaneously check the validity of an email address as a user types it. If a typo or an invalid domain is detected, the user receives an immediate prompt to correct their details. This significantly minimizes the influx of bad data into the CRM and marketing automation systems, preventing issues before they even begin and directly addressing potential "hand-off anxieties" between marketing and sales. -
Bulk Verification:
For existing email lists, particularly those that have accumulated over time, bulk verification is essential. This involves uploading an entire list to a verification service, which then processes and cleanses it. Even a list that was pristine six months ago will naturally decay. Data decay rates vary by industry, but can range from 20-30% annually, especially in dynamic sectors like B2B where job changes, company closures, and domain expirations are common. Bulk verification helps improve the data integrity of these legacy lists, preparing them for new campaigns and ensuring historical data remains valuable. -
Regular Maintenance:
Data hygiene should be a scheduled, routine part of email marketing operations, not an occasional emergency task. By making verification a regular maintenance activity, organizations can catch invalid addresses before their next send, reducing hard bounces and consistently improving deliverability. The ideal cadence for verification depends on the organization’s unique needs and industry velocity. High-velocity industries like SaaS or e-commerce, with rapid lead churn, may require monthly or quarterly verification, while others might suffice with semi-annual or annual checks. -
Verify Before Sending Major Campaigns:
It is always a best practice to perform a comprehensive verification of your email list before launching any major seasonal campaign (e.g., Black Friday, holiday promotions, product launches) or high-stakes announcements. These campaigns often represent significant revenue opportunities, and ensuring the most up-to-date, clean list is paramount for maximizing deliverability and driving campaign success when it matters most.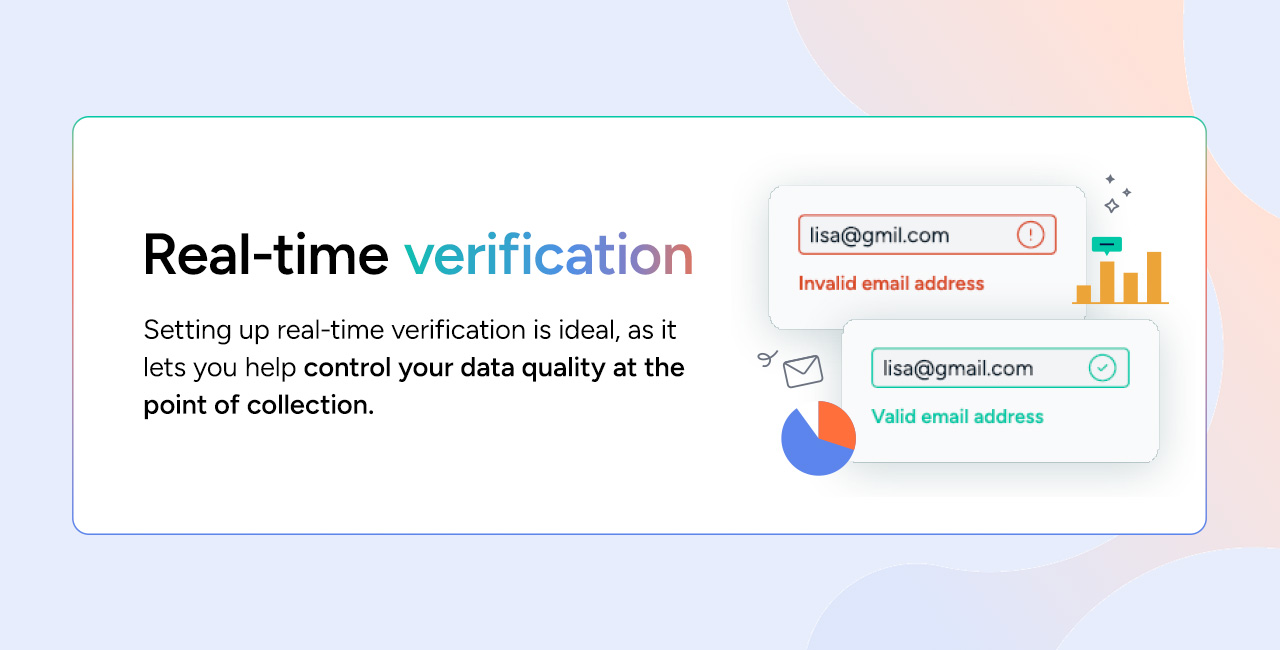
-
Managing the "Unknowns":
Email verification tools sometimes return a small percentage of results with an "unknown" status. This can occur due to server timeouts, overly strict security settings on recipient mail servers, or other transient network issues. A common but risky mistake is to treat these unknowns as valid and include them in regular campaigns, which can inadvertently increase bounce rates. A more strategic approach is to segment these contacts onto a "quarantine list." These contacts can then be tested with low-volume, text-only re-engagement emails sent from a secondary sending Internet Protocol (IP) address. This strategy protects the primary sender’s reputation while attempting to recover genuinely interested leads, effectively turning potential liabilities into valuable assets.
Industry Standard: Validity BriteVerify’s Role in Precision Email Marketing
When selecting an email verification partner, speed, accuracy, and scalability are paramount. Validity’s BriteVerify email verification solution has emerged as an industry standard, trusted by tens of thousands of organizations globally, precisely because it consistently delivers on these critical fronts, significantly improving customer data quality.
BriteVerify is engineered to handle massive volumes of data without introducing latency. This capability is crucial for real-time verification APIs, ensuring that the user experience on web forms remains seamless and fast, without any noticeable slowdowns. Whether processing thousands of leads per hour at the point of capture or validating millions of records in a bulk batch, the tool scales effortlessly to meet diverse operational demands.
The accuracy of email verification hinges on the quality and reach of the provider’s network. BriteVerify distinguishes itself through its deep, established relationships with major inbox providers and its expansive global data network. This proprietary advantage allows for more precise and reliable status checks compared to competitors who may rely on less robust methods like data scraping. By minimizing the number of "unknown" results in email lists, BriteVerify enables organizations to retain a higher percentage of valid leads while systematically eliminating problematic data that could adversely affect sender reputation. This precision reduces ambiguity and allows for more confident decision-making regarding list management.
Furthermore, BriteVerify is designed for seamless integration into existing marketing automation platforms, CRM systems, and other enterprise applications. This ease of onboarding minimizes technical headaches and accelerates the time-to-value, allowing organizations to quickly implement and benefit from improved data hygiene without disruptive overhauls to their current tech stack.
Maximize Every Send with BriteVerify
Prioritizing email verification transforms it from a technical chore into a strategic imperative, empowering creative teams to leverage their resources with unparalleled efficiency. Once an organization operates with trusted, validated data, the focus can squarely shift to innovation, optimization, and truly impactful engagement strategies. Validity’s BriteVerify offers a flexible and powerful solution, allowing organizations to verify their lists proactively at the point of capture, through regular bulk validations, or strategically before critical campaigns. This multi-faceted approach systematically protects sender reputation, maximizes deliverability, and ensures that every email reaches an interested lead, ultimately driving higher engagement and superior business outcomes. By integrating robust email verification, companies are not just cleaning their lists; they are fortifying their entire digital marketing ecosystem.