In an era where digital acquisition costs are under constant scrutiny, Raiffeisen Bank’s Russian division recently faced a significant challenge that threatened the integrity of its marketing budget and the accuracy of its performance metrics. The financial institution, a prominent player in the Russian banking sector, observed a troubling trend: while the costs associated with its affiliate marketing programs—specifically those operating on a Cost Per Action (CPA) model—were rising at an abnormal rate, the corresponding revenue remained stagnant. This discrepancy prompted a deep-dive investigation into the bank’s traffic sources, eventually revealing a sophisticated scheme of affiliate fraud executed through browser extensions.
The investigation, conducted in partnership with the data analytics firm OWOX BI, highlighted a growing vulnerability in the digital advertising ecosystem. As financial institutions increasingly rely on third-party affiliates to drive high-value conversions, such as credit card applications and loan inquiries, the incentive for malicious actors to manipulate attribution data has intensified. For Raiffeisen Bank, the solution required moving beyond standard web analytics to a more granular, hit-level data processing environment.
The Mechanism of Source Substitution Fraud
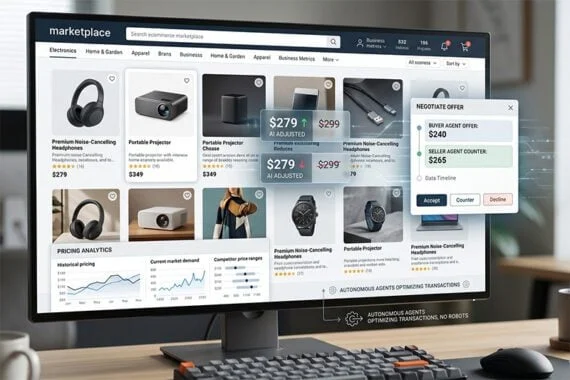
The primary suspicion held by Raiffeisen’s marketing team was that certain affiliates were utilizing "cookie stuffing" or "source rewriting" tactics. This specific form of fraud often involves the use of seemingly benign browser extensions, such as those offering price comparisons, discount codes, or cashback notifications.
When a user navigated to the Raiffeisen Bank website and began filling out an application form, these malicious extensions would trigger a pop-up window offering a discount or a promotional deal. If the user clicked the link within this pop-up, the extension would execute a script to refresh the page or redirect the user, effectively injecting the affiliate’s tracking parameters into the user’s session cookies.
This maneuver has a two-fold negative impact. First, it breaks the user’s current session, often causing technical glitches or forcing the user to restart the application process, which negatively affects the user experience. Second, and more critically for the bank’s finances, it overwrites the original traffic source—such as organic search or a paid search (CPC) campaign—with the affiliate’s ID. Consequently, when the user completes the transaction, the affiliate is credited with a conversion they did not genuinely earn, leading the bank to pay a commission for traffic it had already acquired through other channels.
Chronology of the Investigation and Technical Implementation
The path to uncovering the fraud was structured across several phases, beginning with the identification of anomalies and concluding with a comprehensive audit of affiliate partners.
Phase 1: Identifying the Anomaly
In the first quarter of the project, Raiffeisen’s Head of Online Sales, Dmitriy Berezin, noted that the CPA channel’s expenditure was outstripping its performance indicators. Internal audits showed that users were frequently experiencing session breaks precisely at the checkout or application stage. This technical "hiccup" was the first red flag, suggesting that external scripts were interfering with the browser environment.
Phase 2: Deploying a High-Resolution Data Pipeline
To prove the hypothesis of source rewriting, the team needed access to raw, unsampled data. Standard Google Analytics (GA) reporting was insufficient because it aggregates data and lacks the hit-level timestamps required to track millisecond-level changes in session behavior.
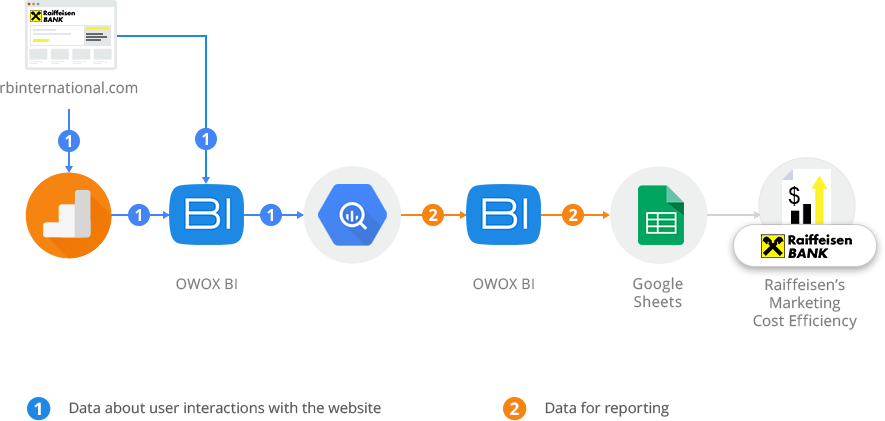
Raiffeisen partnered with OWOX BI to implement a data streaming pipeline. Using the OWOX BI Pipeline, the bank began exporting raw website data directly into Google BigQuery. This setup allowed for the collection of every "hit" (interaction) in near real-time, complete with precise timestamps and unique client identifiers. This level of detail is compliant with high-tier security standards, a non-negotiable requirement for a global financial institution like Raiffeisen.
Phase 3: Analytical Modeling and Filtering
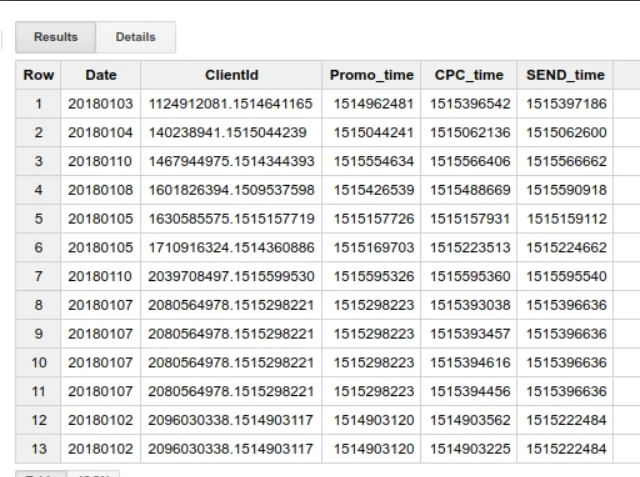
Once the data was flowing into Google BigQuery, Victoriia Pashchenko and the OWOX BI analytical team developed SQL queries to isolate fraudulent patterns. The analysis focused on three specific criteria to identify "robbed" transactions:
- Session Continuity: Identifying instances where a user had two distinct sessions on the same page within a very short timeframe (less than 60 seconds).
- Source Alteration: Filtering for cases where the first session was attributed to "Organic" or "CPC" and the immediate subsequent session was attributed to a "CPA" affiliate.
- Transaction Mapping: Matching these session-switch events to successful conversions or completed application forms.
Supporting Data and Evidence of Fraud
The data gathered through the BigQuery environment provided the "smoking gun" needed to take action. The analysts generated reports that tracked the exact sequence of user actions.
For example, a typical fraudulent sequence identified in the data showed a user arriving via a Google search (Organic). At 14:00:05, the user is on the application page. At 14:00:45, a new session starts on the exact same URL, but the source has changed to a specific CPA affiliate. At 14:02:00, the application is submitted.
By aggregating this data into pivot tables, Raiffeisen was able to quantify the damage. The reports revealed:
- The Volume of Stolen Attributions: A significant percentage of transactions previously credited to CPA networks were, in fact, originally sourced from organic search or paid search campaigns.
- Affiliate Culprits: The data allowed the bank to pinpoint exactly which affiliate IDs were associated with these rapid session breaks.
- Financial Impact: The bank could calculate the exact amount of "overbilling" by comparing the commissions claimed by affiliates against the transactions where source rewriting was detected.
In one analyzed segment, it was discovered that two specific partners were responsible for the vast majority of the rewritten sources. These partners had successfully "robbed" the organic and CPC channels of dozens of high-value conversions by intercepting users at the very end of the conversion funnel.
Official Response and Strategic Reallocation
Following the presentation of this data, Raiffeisen Bank took immediate corrective measures. The institution terminated its cooperation with the two dishonest affiliate partners identified in the report. By removing these entities from their CPA network, the bank not only reduced its immediate marketing spend but also improved the accuracy of its attribution modeling.

Dmitriy Berezin emphasized that this was not just about saving money, but about the integrity of the bank’s digital strategy. "By bringing these cases of fraud to light, we managed to optimize the ad budget and ensure that our resources are being directed toward partners who provide genuine value," Berezin noted during a review of the project.
The bank has since integrated this monitoring system into its regular marketing operations. By using the OWOX BI and Google BigQuery setup, Raiffeisen now maintains an ongoing "fraud dashboard" that flags suspicious session breaks in real-time, allowing the marketing team to challenge suspicious invoices from CPA networks before payments are processed.
Broader Industry Implications and Analysis
The Raiffeisen Bank case study serves as a critical warning for the broader digital marketing industry. Ad fraud is a multi-billion dollar problem, with some estimates suggesting that global losses to ad fraud could reach $100 billion by 2024. The specific tactic of using browser extensions to rewrite cookies is particularly insidious because it targets users who are already deep in the conversion funnel—the "last mile" of the customer journey.
The Vulnerability of the CPA Model
While the Cost Per Action model is often touted as a "risk-free" way for advertisers to pay only for results, it creates a perverse incentive for affiliates. Because they only get paid if a transaction occurs, the pressure to "claim" existing transactions is high. Without sophisticated tracking, many companies may be paying for the same customer twice: once to acquire them via search ads and a second time in the form of a fraudulent affiliate commission.
The Shift Toward Raw Data Ownership
This case underscores a significant shift in the role of the web analyst. Standard, out-of-the-box analytics tools are no longer sufficient for security and fraud prevention. Modern marketers must act as data engineers, ensuring they have ownership of raw, hit-level data. The ability to join disparate datasets—such as website behavior, CRM data, and affiliate logs—within a cloud warehouse like BigQuery is becoming a standard requirement for enterprise-level fraud detection.
Future Outlook for Affiliate Transparency
As financial institutions like Raiffeisen lead the way in data-driven fraud detection, affiliate networks will likely face increased pressure to vet their sub-affiliates more rigorously. The use of browser extensions for "in-session" marketing is increasingly being viewed as a violation of terms of service across many major affiliate platforms.
In conclusion, Raiffeisen Bank’s proactive approach demonstrates that while digital fraud is becoming more sophisticated, the tools available to combat it are also evolving. By leveraging raw data and advanced cloud processing, the bank successfully protected its marketing budget, ensured a smoother user experience for its customers, and set a new benchmark for transparency in the Russian affiliate marketing landscape. The project serves as a blueprint for other organizations seeking to validate their marketing spend and reclaim control over their digital attribution.