In an era defined by pervasive digital communication, the integrity and security of email have become paramount, pushing the once-obscure technical discipline of email authentication to the forefront of cybersecurity and marketing strategy. While often perceived as a complex labyrinth of acronyms and protocols, email authentication is, at its core, the digital security measure that ensures each message arriving in an inbox is genuinely from the claimed sender, has not been tampered with in transit, and adheres to the sender’s stated policies for handling fraudulent messages. This foundational layer of trust is no longer optional; it is a critical requirement for any entity sending email, particularly in the wake of stringent new mandates from major mailbox providers.
The Escalating Need for Email Security
The digital landscape is increasingly fraught with sophisticated cyber threats, with email remaining the primary vector for attacks such as phishing, spoofing, and business email compromise (BEC). Reports consistently highlight the staggering volume of email traffic—billions of messages exchanged daily—and the corresponding surge in malicious activity. According to the Anti-Phishing Working Group (APWG), the number of phishing attacks reached unprecedented levels in recent years, underscoring the urgent need for robust defense mechanisms. Without proper authentication, a legitimate sender’s domain can be easily impersonated, leading to devastating consequences for brand reputation, customer trust, and financial security. For recipients, the sheer volume of unsolicited and fraudulent emails degrades the overall inbox experience, making it harder to identify and engage with genuine communications. This dual pressure—the need to protect users from harm and to ensure legitimate messages reach their intended audience—has driven a collective effort among industry leaders to bolster email security standards.
The Genesis of Email Authentication Standards
The foundational principles of email authentication were forged through collaborative efforts by various groups, including the Internet Engineering Task Force’s (IETF) Anti-Spam Research Group, alongside pioneering companies like Yahoo and Cisco. These organizations recognized early on the inherent vulnerabilities of the Simple Mail Transfer Protocol (SMTP), which was not originally designed with robust sender verification in mind. In its nascent stages, email was largely an open system, making it easy for malicious actors to forge sender addresses. The mid-2000s saw the emergence of the first widely adopted standards, primarily to combat the growing menace of spam and email-based fraud. These initial efforts laid the groundwork for what would evolve into the sophisticated suite of authentication technologies safeguarding email today. The journey from basic sender verification to comprehensive policy enforcement reflects an ongoing arms race against cybercriminals, necessitating continuous innovation and widespread adoption of these protocols.
Mailbox Providers Take a Stand: A New Era of Enforcement
The most significant recent development in email authentication has been the unequivocal stance taken by leading mailbox providers (MBPs) such as Google (Gmail), Yahoo, and Microsoft. These giants, collectively handling the vast majority of global email traffic, have declared that proper email authentication is no longer a best practice but a mandatory prerequisite for successful deliverability.
Chronology of Mandates:
- October 2023: Google and Yahoo jointly announced new, stricter email sender requirements. These mandates were framed as a crucial step to protect users from unwanted and malicious emails, aiming to significantly reduce spam and enhance inbox security.
- February 2024: Key aspects of the new requirements began to take effect. For bulk senders (defined by Google and Yahoo as those sending more than 5,000 emails to Gmail/Yahoo addresses in a single day), this included the necessity of implementing DMARC with at least a
p=nonepolicy, ensuring easy one-click unsubscribe options, and maintaining a low spam complaint rate. - April 2024: Google commenced progressively rejecting non-compliant traffic. Senders failing to meet the foundational authentication standards (SPF, DKIM, DMARC) started experiencing significant deliverability issues, including messages being bounced or routed directly to spam folders.
- Late 2025 (and ongoing): Non-compliant senders face the prospect of temporary and, eventually, permanent rejections. This phased approach allows senders time to adapt but signals a firm commitment to enforcement. Microsoft has adopted a similarly rigorous approach, aligning its bulk email rules to ensure a safer inbox environment for its users.
The rationale behind these mandates is multi-faceted. Beyond combating phishing and spam, MBPs aim to improve the overall user experience by ensuring that legitimate communications are reliably delivered, while fraudulent messages are effectively blocked. This move also places greater accountability on senders to adopt responsible email practices, shifting the burden of filtering away from individual users and onto the infrastructure level. As Google stated in its official communication, "These changes will help foster a safer and more trustworthy email ecosystem for everyone."
Deciphering the Core Authentication Protocols
The email ecosystem relies on five core authentication technologies working in concert to safeguard messages on their journey to the inbox: Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), Domain-based Message Authentication, Reporting & Conformance (DMARC), Authenticated Received Chain (ARC), and Brand Indicators for Message Identification (BIMI). Understanding each is crucial for any sender aiming for optimal deliverability and brand protection.
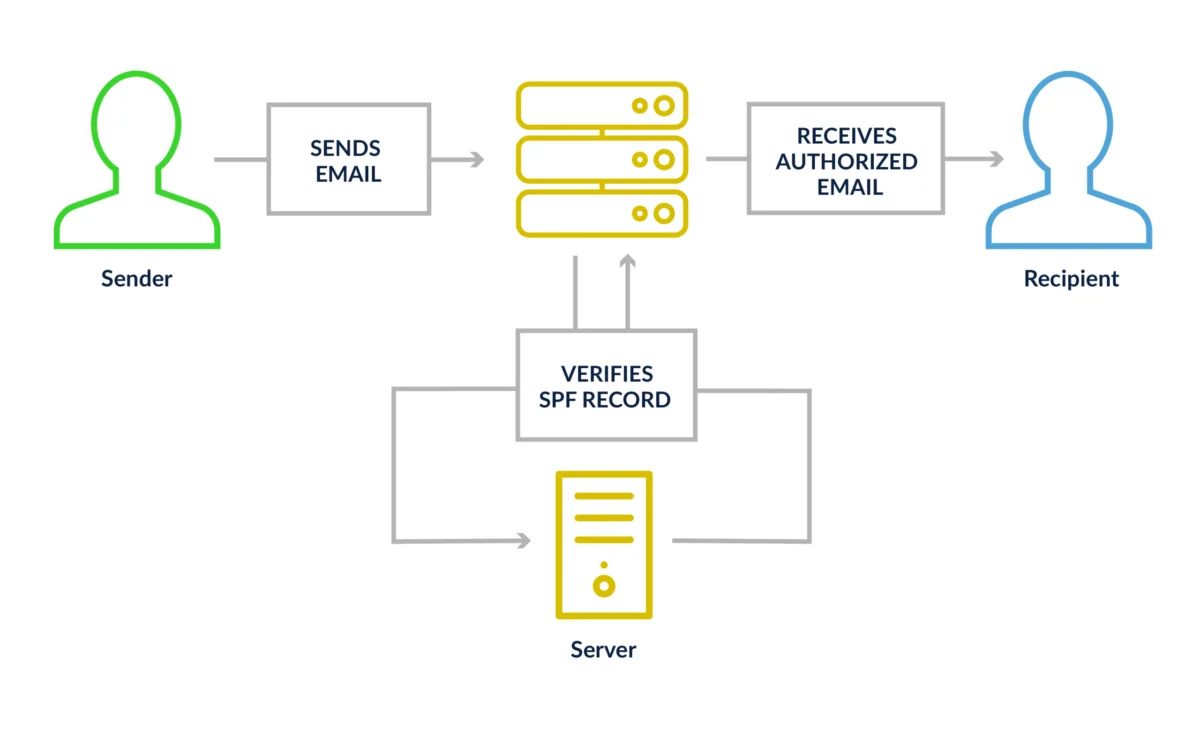
Sender Policy Framework (SPF)
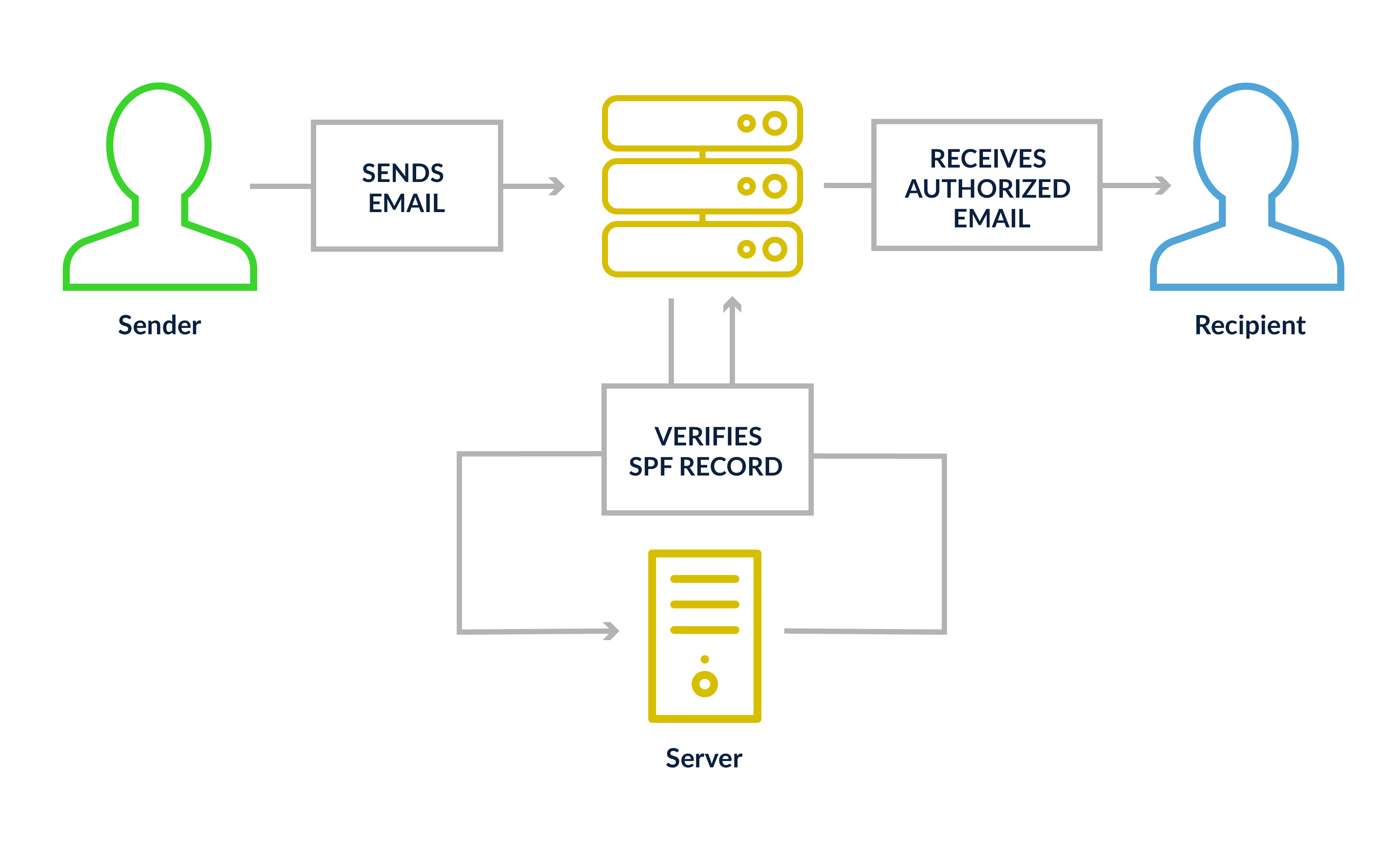
SPF: The Guest List for Your Domain
SPF acts as a digital guest list for your domain, specifying which IP addresses are authorized to send email on your behalf. When a mail server prepares to send a message, the sending domain publishes an SPF record within its Domain Name System (DNS). This TXT record contains a list of approved IP addresses or domains (often including those of third-party email service providers, or ESPs). Upon receiving an email, the recipient’s mail server performs an SPF check, querying the sender’s DNS record to verify if the originating IP address is on the approved list. If the IP address is not listed, the receiving server knows something is amiss.
Technical Nuances and Best Practices:
An SPF record can include individual IP addresses, IP ranges, or references to other domains (using the include mechanism). Senders can also define enforcement levels:
+all: Pass (rarely used due to security risks)~all: Soft fail (message accepted but flagged as suspicious)-all: Fail (message rejected or quarantined)
Most reputable senders opt for ~all or -all to indicate stricter enforcement. A common pitfall with SPF is the "permerror" caused by exceeding the 10-DNS-lookup limit. Each include statement counts as a lookup. Exceeding this limit can cause SPF to fail entirely, rendering the authentication ineffective. Senders must regularly audit their SPF records, especially when adding or removing third-party sending services, to ensure compliance and avoid this critical error.
DomainKeys Identified Mail (DKIM)
DKIM: The Tamper-Evident Seal
DKIM provides a cryptographic signature for outgoing emails, akin to a tamper-evident seal on a package. When your mail server dispatches a message, it generates a unique cryptographic signature using a private key and embeds this signature in the email header. A corresponding public key is published in your domain’s DNS records. Upon receiving the email, the recipient’s server retrieves the public key from your DNS and uses it to verify the signature. If any part of the email’s content (headers or body) has been altered in transit, the signature validation will fail, indicating potential tampering or forgery.
Technical Nuances and Best Practices:
DKIM signatures are designed to be robust against minor changes that occur during forwarding, provided the signed parts of the email remain intact. However, significant modifications can break the signature. For optimal security, DKIM keys should be at least 2048 bits in length. Older 1024-bit keys are increasingly vulnerable to cryptographic attacks and no longer meet modern security standards. While many ESPs manage DKIM key configuration automatically, it is crucial for senders to confirm that their platform is using appropriately strong keys.
Domain-based Message Authentication, Reporting & Conformance (DMARC)
DMARC: The Security Policy Officer
DMARC builds upon SPF and DKIM, acting as the overarching policy framework that dictates how receiving mail servers should handle emails that fail SPF or DKIM checks. Critically, DMARC introduces the concept of "alignment." For DMARC to pass, the domain in the email’s visible "From" address must align (either exactly or with a subdomain) with the domain validated by SPF or DKIM. Without this alignment, DMARC fails, even if the underlying SPF or DKIM checks passed.
Enforcement Policies and Reporting:
DMARC offers three policy levels, allowing senders to progressively increase enforcement:
p=none: Monitor only. No action is taken on failing messages, but aggregate reports are generated. This is the minimum requirement for bulk senders under the new MBP mandates.p=quarantine: Messages failing DMARC are sent to the recipient’s spam or junk folder.p=reject: Messages failing DMARC are blocked entirely and not delivered to the recipient.
The ultimate goal for senders is to reach p=quarantine or p=reject to maximize protection against impersonation. A significant advantage of DMARC is its reporting capability. Mailbox providers send daily aggregate reports (RUA records) to specified email addresses, detailing which messages passed or failed authentication, the IP addresses involved, and the reasons for failure. These reports are invaluable for identifying legitimate sending sources, detecting unauthorized sending, and catching spoofing or phishing attempts against the domain. This forensic data allows organizations to continuously refine their email sending practices and security posture.
Authenticated Received Chain (ARC)
ARC: The Chain of Custody for Forwarded Email
ARC addresses a specific challenge in email authentication: the problem of legitimate messages failing DMARC after being forwarded or modified by intermediate systems. When an email passes through a mailing list processor, a security gateway, or another forwarding service, these systems may alter the message (e.g., adding a footer, modifying headers). Such changes can inadvertently break a valid DKIM signature, leading to a DMARC failure even if the original message was perfectly legitimate.
ARC acts as a "chain of custody," preserving the original authentication results. Each intermediate server that handles an ARC-enabled message logs and digitally signs the authentication results it observed before passing the message along. When the email reaches its final destination, the receiving server can examine this ARC chain. If the DMARC check fails due to intermediate modifications, the server can still see that the message started its journey properly authenticated, preventing it from being incorrectly flagged as fraudulent. Unlike SPF, DKIM, and DMARC, ARC is not something individual senders configure directly; it is implemented by the mail servers in the middle of the delivery chain. However, understanding its function is vital for comprehending why forwarded emails might behave differently in terms of authentication.
Brand Indicators for Message Identification (BIMI)
BIMI: The Visual Trust Signal
BIMI is the newest addition to the authentication suite, offering a powerful visual trust signal: the display of a brand’s verified logo directly in the recipient’s inbox, even before the email is opened. This immediate brand recognition helps subscribers quickly identify legitimate emails and enhances engagement.
Implementation Prerequisites and Certificates:
To implement BIMI, a sender must have SPF, DKIM, and DMARC fully configured, with the DMARC policy set to an enforcement level (p=quarantine or p=reject). A p=none DMARC policy is insufficient for BIMI. Once these prerequisites are met, the sender publishes a BIMI DNS record pointing to a properly formatted Scalable Vector Graphics (SVG) version of their logo.
Certificates: VMC vs. CMC
- Verified Mark Certificate (VMC): The original and most robust certification option. VMCs require the brand’s logo to be a registered trademark and are issued by authorized Certificate Authorities (e.g., DigiCert). A VMC unlocks full BIMI support, including logo display and, notably, a blue checkmark in Gmail, signifying a highly verified sender.
- Common Mark Certificate (CMC): A newer, more accessible option introduced in 2024. CMCs do not require a registered trademark, only proof that the logo has been publicly displayed for at least 12 months. While CMC holders gain logo display in Gmail, they do not receive the coveted blue checkmark, which remains exclusive to VMC-certified brands. The introduction of CMCs significantly broadens BIMI accessibility, especially for smaller businesses or those with non-trademarked logos.
MBP Support at a Glance:
- Gmail: Supports BIMI with both VMC (including blue checkmark) and CMC (logo only).
- Yahoo Mail: Supports BIMI with VMC.
- Apple Mail: Supports BIMI with VMC.
- Other MBPs: Support is growing, with various providers implementing BIMI to differing extents.
Implications for Senders and the Digital Ecosystem
The recent mandates and the evolving landscape of email authentication have profound implications across the digital ecosystem.
Deliverability and Return on Investment (ROI)
For businesses, the direct link between email authentication and deliverability is undeniable. Without proper SPF, DKIM, and DMARC implementation, emails are increasingly likely to be filtered into spam folders or outright rejected by major MBPs. This directly impacts marketing campaigns, transactional emails, and critical customer communications. A high bounce rate or low inbox placement translates directly to lost opportunities, diminished engagement, and a reduced return on investment from email efforts. As senders navigate these new requirements, proactive compliance becomes a competitive advantage, ensuring their messages reach their intended audience and drive desired outcomes.
Brand Protection and Customer Trust
Robust email authentication is a powerful shield against brand impersonation. Phishing and spoofing attacks, which leverage fake sender identities, can severely damage a brand’s reputation and erode customer trust. By implementing DMARC with an enforcement policy, brands can significantly reduce the success rate of such attacks, reassuring customers that emails from their domain are genuine. BIMI further amplifies this, providing a visual cue of authenticity that builds instant recognition and trust. In a world where digital identity theft is rampant, safeguarding one’s sending domain is as crucial as protecting physical assets.
Operational Demands and Resource Allocation
Achieving and maintaining robust email authentication requires a sustained commitment. It is not a one-time technical fix but an ongoing process of configuration, monitoring, and adaptation. Organizations must invest in the necessary technical expertise, whether in-house or through external partners, to correctly configure DNS records, manage DKIM keys, and interpret DMARC reports. The need to regularly review SPF records, particularly when integrating new third-party services, and to monitor DMARC aggregate reports for anomalies demands dedicated resources. This operational demand underscores that email security has matured from a purely IT function to a critical business imperative.
The Future of Email Security: A Continuous Journey
Email authentication, while foundational, is not the finish line in the race for email security. The threat landscape is constantly evolving, requiring continuous vigilance and adaptation. The trend towards stricter enforcement by MBPs is likely to continue, pushing senders towards even more rigorous authentication and reputation management practices. Emerging technologies and standards will continue to refine how email is verified and trusted.
In conclusion, the era of optional email authentication is decisively over. With Gmail, Yahoo, and Microsoft unequivocally enforcing these requirements for all senders, particularly bulk senders, compliance is no longer a matter of best practice but a fundamental necessity. Getting SPF, DKIM, and DMARC correctly configured is the non-negotiable starting point. Progressing DMARC policies towards enforcement, diligently monitoring aggregate reports, and strategically adopting BIMI are all essential steps toward cultivating a more secure, trusted, and ultimately, more effective email program. While the technical complexities can be daunting, the payoff—enhanced deliverability, fortified brand reputation, and unwavering customer trust—is unequivocally worth the investment. Tools like Litmus, which offer infrastructure checks, can assist organizations in ensuring their email authentication protocols are robust and compliant, paving the way for a more reliable and secure digital communication future.