The digital landscape of email communication is undergoing a profound transformation, driven by an escalating need for security and trust. If the concept of email deliverability has ever crossed your professional radar, the term "email authentication" has undoubtedly surfaced. Far from mere technical jargon, email authentication represents the foundational digital security measures that ensure the legitimacy and integrity of every message dispatched. Its significance to an organization’s email program, encompassing everything from marketing campaigns to critical transactional notifications, has never been more pronounced, particularly in light of recent stringent mandates from major mailbox providers.
As highlighted by email expert Dela Quist during a recent "Email After Hours" podcast, email authentication is the bedrock upon which reliable digital communication is built. It’s a multi-layered defense mechanism designed to verify the sender’s identity, confirm that the message hasn’t been tampered with in transit, and ultimately, determine how receiving mail servers should treat an incoming email. This rigorous verification process is crucial for combating the pervasive threats of spam, phishing, and domain spoofing, which cost businesses billions annually and erode user trust.
The genesis of modern email authentication standards can be traced back to collaborative efforts by various influential groups, including the IETF’s Anti-Spam Research Group, technology giants like Yahoo, and cybersecurity leaders such as Cisco. These pioneers laid the groundwork for the robust protocols that protect email today. Over time, these foundational policies have evolved into five core authentication technologies that work in concert to safeguard emails on their journey to the inbox: Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), Domain-based Message Authentication, Reporting & Conformance (DMARC), Authenticated Received Chain (ARC), and Brand Indicators for Message Identification (BIMI). While these acronyms may initially appear daunting, understanding their individual roles and collective power is essential for any entity serious about its email presence.
The Mandate Shift: A New Era for Email Deliverability
The era of optional email authentication has definitively concluded. Major mailbox providers (MBPs) such as Gmail, Yahoo, and Microsoft have unequivocally stated their commitment to enhancing user security and inbox integrity. Their recent, comprehensive mandates have fundamentally reshaped the landscape for email senders globally, cementing proper authentication as a non-negotiable requirement. These directives, designed to drastically reduce the volume of unsolicited and fraudulent email, signify a collective industry push towards a more secure and trustworthy email ecosystem.
The expectations now placed upon all senders, irrespective of their volume, are clear and universally applicable:
- Implement Strong Authentication: All senders must authenticate their emails using at least SPF or DKIM.
- Establish a DMARC Policy: Senders, especially bulk senders, are required to publish a DMARC policy for their sending domains. While a
p=none(monitoring) policy is the minimum starting point, the clear industry trend and recommendation is to move towardsp=quarantineorp=rejectfor full protection. - Maintain Low Spam Rates: Senders must keep their spam complaint rates exceptionally low, typically below 0.1% (and ideally below 0.03%), to avoid negative sender reputation and delivery issues.
- Provide Easy Unsubscribe Mechanisms: Bulk senders must offer a one-click unsubscribe option in their emails and honor unsubscribe requests promptly, ideally within two days.
For reputable organizations that depend on email to connect with their subscribers and customers, adherence to these requirements is paramount. There are no viable shortcuts. Gmail, for instance, began progressively rejecting non-compliant traffic in April 2024, with more severe penalties, including temporary and permanent rejections, slated for non-compliant senders by late 2025. Yahoo and Microsoft have adopted similarly resolute stances, signaling a unified front against email abuse. Failure to comply directly impacts deliverability, leading to messages being routed to spam folders or outright blocked, severely hindering communication efforts and potentially damaging brand reputation.
Understanding the Pillars of Email Authentication
To navigate this new environment successfully, a detailed understanding of each core authentication method is critical. These technologies, though technically intricate, can be grasped through relatable analogies.
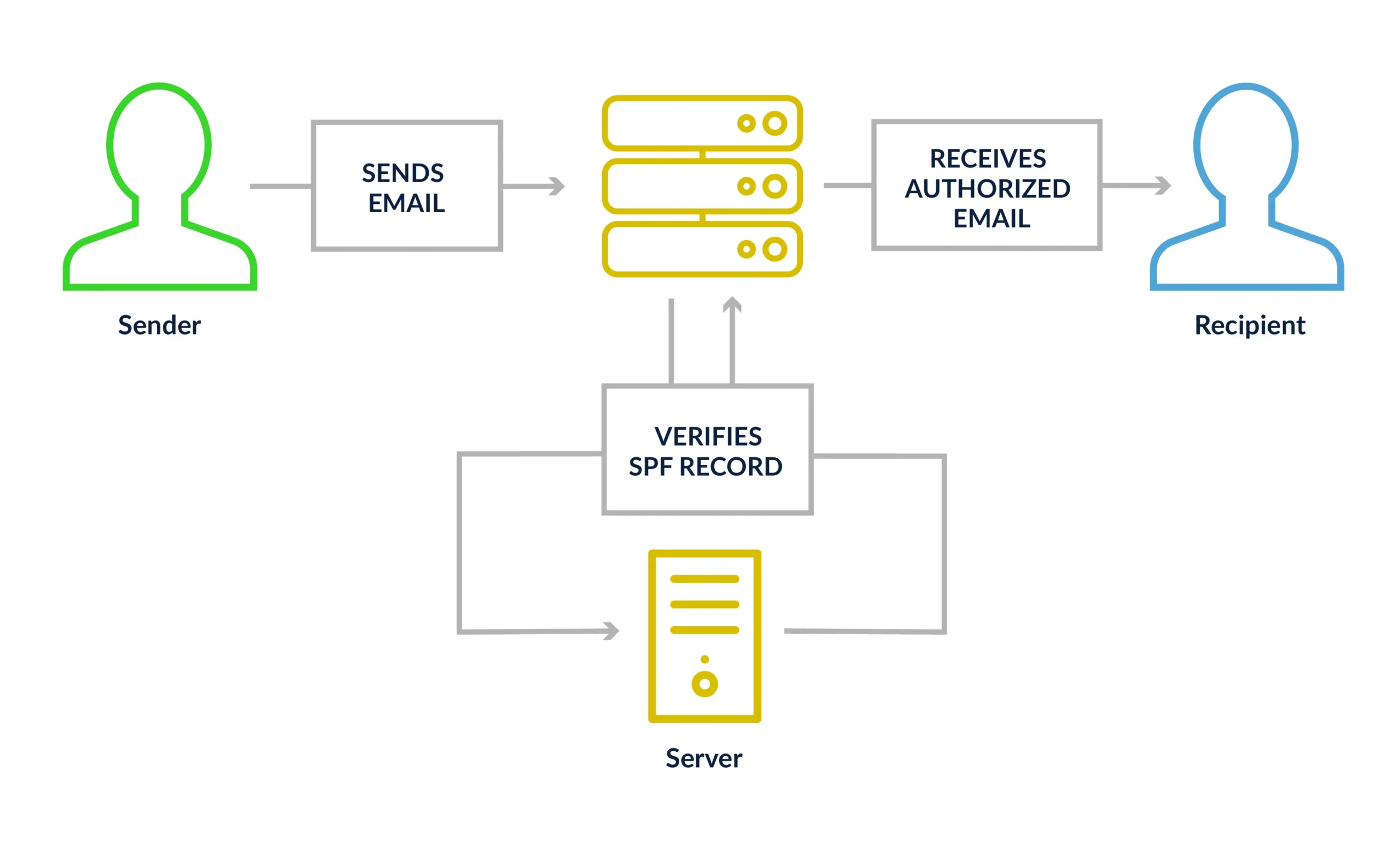
Sender Policy Framework (SPF)
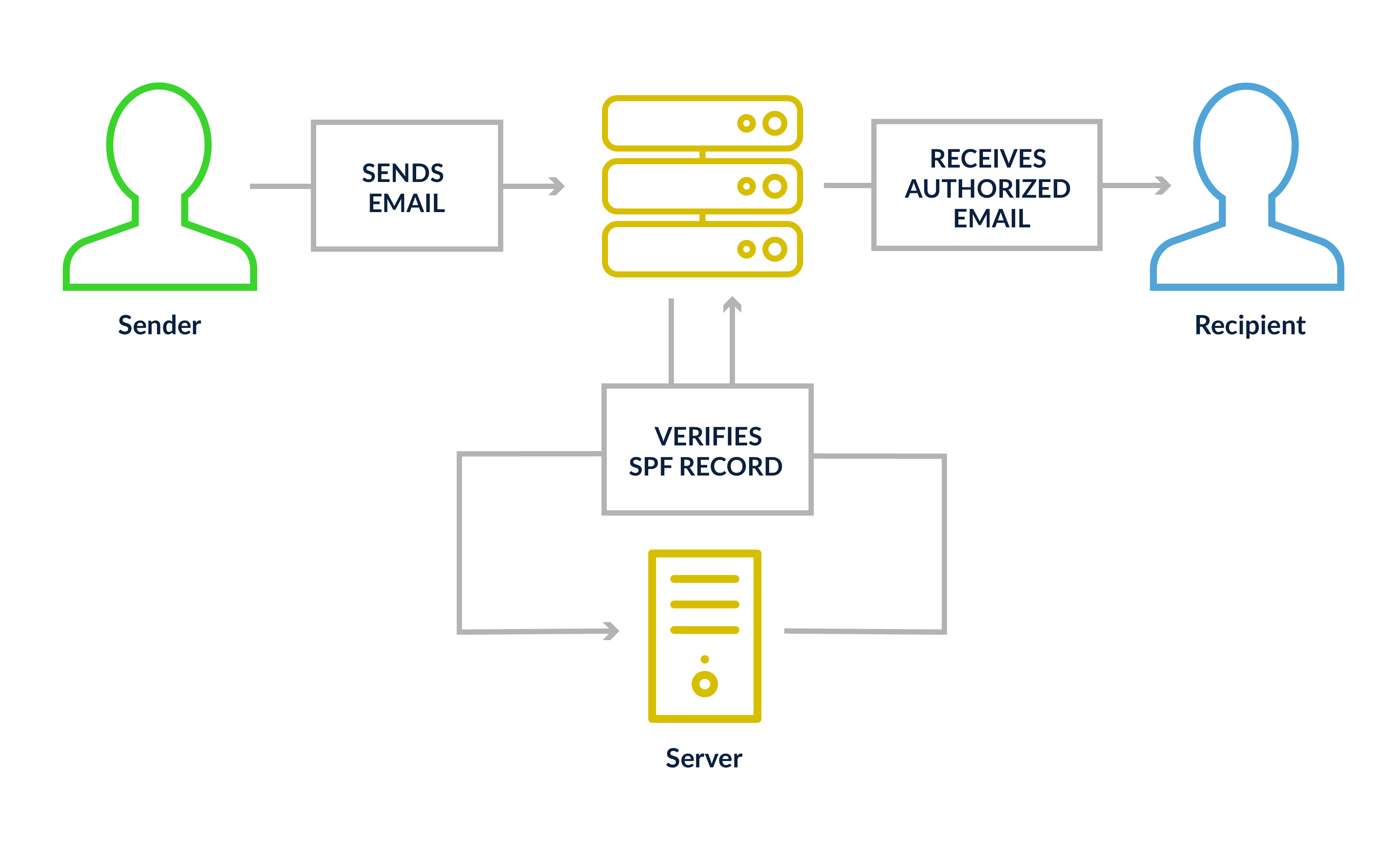
Imagine SPF as the bouncer at an exclusive club, equipped with a meticulously vetted guest list. When an email originates from your domain, your domain’s DNS record publishes a specific SPF record that explicitly lists all authorized IP addresses permitted to send email on your behalf. Upon receiving an email, the recipient’s mail server consults this SPF record. If the email’s originating IP address is not on the approved list, the receiving server immediately flags it as suspicious, indicating an unauthorized attempt to send mail from your domain.
An SPF record can be configured to include individual IP addresses, defined IP ranges, or references to approved third-party sending services, such as your Email Service Provider (ESP). Crucially, senders can also specify enforcement levels within their SPF records:
+all(Pass): All messages from your domain are legitimate, regardless of origin (rarely used due to security risks).~all(Soft Fail): Messages from unauthorized IPs may be legitimate but should be viewed with suspicion. This is a common starting point.-all(Fail): Messages from unauthorized IPs are definitively illegitimate and should be rejected. This offers the highest level of protection.
A critical technical consideration for SPF is the "10-lookup limit." Each time an SPF record uses an include mechanism to reference another domain’s SPF record (e.g., your ESP’s SPF record), it counts as a DNS lookup. Exceeding this limit results in an SPF "permerror" (permanent error), rendering the SPF record invalid and potentially causing all emails from that domain to fail SPF authentication. Proactive management and flattening of SPF records are often necessary for complex sending infrastructures.
DomainKeys Identified Mail (DKIM)
DKIM functions akin to a tamper-evident seal on a secure package. When your mail server dispatches a message, it digitally "stamps" the email with a unique cryptographic signature generated using a private key known only to your sending infrastructure. The corresponding public key is published in your domain’s DNS records. When a receiving server acquires your email, it retrieves the public key from your DNS and uses it to verify the cryptographic signature. If any part of the email (headers or body) has been altered in transit, the signature will not match the public key, causing DKIM to fail. This mechanism guarantees message integrity and sender authenticity.
A vital setup note for DKIM involves key length. Modern security standards mandate a minimum key length of 2048 bits. Older 1024-bit keys are now considered vulnerable and may not be accepted by all MBPs, potentially leading to authentication failures. While most reputable ESPs manage DKIM key generation and rotation, it is prudent for senders to confirm their keys meet current security benchmarks.
Domain-based Message Authentication, Reporting & Conformance (DMARC)
If SPF is the guest list and DKIM is the tamper seal, DMARC acts as the overarching policy framework that dictates the actions to be taken when either SPF or DKIM flags an issue. More importantly, DMARC introduces a crucial element: "alignment." For DMARC to pass, the domain displayed in the "From" address (the one users see) must align with (either strictly or loosely match) the domain used in the SPF record (the "Return-Path" or "Mail From" domain) or the domain used to sign the DKIM record. Without this alignment, DMARC will fail, even if the underlying SPF or DKIM checks initially passed. This prevents sophisticated spoofing where a legitimate SPF/DKIM record might be used for a visually deceptive "From" address.
DMARC policies offer three levels of enforcement, which instruct receiving servers on how to handle emails that fail authentication:
p=none(Monitor): This policy provides valuable insight into email authentication failures without taking any action on the messages. It’s the recommended starting point for new DMARC implementations and the minimum requirement for bulk senders by Google, Yahoo, and Microsoft.p=quarantine(Spam Folder): Messages failing DMARC authentication are directed to the recipient’s spam or junk folder. This significantly reduces the visibility of fraudulent emails.p=reject(Block Entirely): Messages failing DMARC are outright blocked and never delivered to the recipient’s inbox or spam folder. This offers the highest level of protection against spoofing and phishing.
Beyond enforcement, DMARC provides an invaluable reporting mechanism. Receiving MBPs send daily aggregate reports (XML format) to the email address specified in the DMARC record. These reports detail which messages passed or failed authentication, the IP addresses involved, and whether alignment was achieved. This data serves as a critical early-warning system, enabling organizations to detect and respond to unauthorized sending, spoofing, or phishing attempts targeting their domain, thereby protecting their brand and recipients.
Authenticated Received Chain (ARC)
ARC addresses a specific challenge inherent in email forwarding and mailing list scenarios. Normally, when an email is forwarded or processed by an intermediary system (such as a mailing list server, a spam filter, or a security gateway), the message content or headers may be altered. These alterations can inadvertently break the original DKIM signature, leading to a DMARC failure, even if the initial message was legitimate and properly authenticated by the original sender.
ARC acts as a "chain of custody" for email authentication. Each intermediate server that modifies and re-sends an email logs and digitally signs the authentication results it observed before passing the message along. This creates a verifiable historical record. By the time the email reaches its ultimate destination, the final receiving server can examine this ARC chain. It can see that the message began its journey properly authenticated, allowing it to override a subsequent DMARC failure caused by legitimate intermediate modifications. This ensures that legitimate forwarded emails or messages from mailing lists are not erroneously blocked. Unlike SPF, DKIM, and DMARC, ARC is not something individual senders configure directly; it is implemented by mail servers and intermediaries in the email delivery path.
Brand Indicators for Message Identification (BIMI)
BIMI represents a significant leap forward in visual trust and brand recognition within the inbox. It allows brands to display their official, verified logo directly in the recipient’s inbox, often alongside the sender’s name, even before the email is opened. This visual cue serves as an instant trust signal, helping subscribers quickly identify legitimate emails from a trusted brand and distinguish them from phishing attempts.
To implement BIMI, a robust email authentication foundation is a prerequisite. Specifically, a sender must have SPF, DKIM, and DMARC fully configured, with their DMARC policy set to an enforcement level of p=quarantine or p=reject. A p=none policy, while useful for monitoring, is insufficient for BIMI adoption due to its lack of active protection against spoofing. Once these prerequisites are met, the brand publishes a BIMI DNS record that points to a properly formatted SVG (Scalable Vector Graphics) version of their logo.
BIMI offers two primary certification options for logo verification:
- Verified Mark Certificate (VMC): This is the original and most stringent certification option, requiring the brand to possess a registered trademark for its logo. VMCs are issued by authorized Certificate Authorities (e.g., DigiCert). Holding a VMC unlocks full BIMI support, including logo display and often a distinctive "blue checkmark" of verification in supporting mailbox providers like Gmail, signifying a higher level of trust.
- Common Mark Certificate (CMC): Introduced more recently, the CMC offers a more accessible pathway to BIMI. It does not require a registered trademark, instead demanding proof that the brand’s logo has been publicly displayed and in consistent use for a minimum of 12 months. Google began accepting CMCs in 2024, significantly expanding BIMI’s reach to a broader array of brands. While CMC holders benefit from logo display in Gmail, the coveted blue checkmark remains exclusively reserved for VMC holders.
MBP support at a glance:
- Gmail: Supports BIMI with VMC (including blue checkmark) and CMC (logo only).
- Yahoo Mail: Supports BIMI with VMC.
- Apple Mail: Supports BIMI with VMC.
- Fastmail: Supports BIMI with VMC.
The adoption of BIMI is steadily increasing, driven by its clear benefits in enhancing brand visibility, improving open rates, and bolstering consumer confidence.
The Evolution of Email Security: A Brief History
The journey to sophisticated email authentication protocols is a direct response to the escalating threats that emerged with the widespread adoption of email. In its nascent stages, email was a relatively open and trusting communication channel. However, as its popularity surged in the late 1990s and early 2000s, it quickly became a primary vector for unsolicited commercial email (spam) and malicious attacks like phishing.
Early attempts to combat spam primarily focused on content filtering and blacklists, which proved reactive and often inefficient against rapidly evolving tactics. The need for proactive, identity-based verification became undeniable. SPF was one of the first widely adopted standards, emerging in the early 2000s, providing a mechanism for senders to declare authorized sending sources. DKIM followed shortly thereafter, adding a layer of cryptographic integrity to messages.
However, a critical gap remained: what should receiving servers do when SPF or DKIM failed, and how could senders gain visibility into these failures? This led to the development of DMARC in 2012, a collaborative effort by major players like Google, Microsoft, Yahoo, and PayPal. DMARC provided the crucial policy layer and reporting functionality that transformed email authentication from a mere technical check into a comprehensive security framework. ARC then addressed the complexities of legitimate message forwarding, and BIMI, the newest addition, focuses on enhancing visual trust and brand recognition. This chronology underscores a continuous arms race against cybercriminals, with authentication standards evolving to meet increasingly sophisticated threats.
The Broader Impact: Why Authentication Matters Beyond Deliverability
Email authentication is far more than a technical compliance exercise; its impact reverberates across an organization’s entire digital footprint, influencing brand reputation, customer trust, and overall cybersecurity posture.
Brand Reputation and Trust: In an age rife with online scams, a verified sending identity is a powerful trust signal. When emails are consistently authenticated, recipients learn to trust messages from that domain, fostering a positive brand image. Conversely, a lack of authentication leaves a brand vulnerable to spoofing, where malicious actors impersonate the brand to defraud customers. Such incidents can cause irreparable damage to reputation, erode customer loyalty, and lead to significant financial and legal repercussions.
Cybersecurity Defense: Strong authentication, particularly DMARC with an enforcement policy, is one of the most effective defenses against phishing and business email compromise (BEC) attacks. These attacks often rely on impersonating legitimate organizations to trick recipients into revealing sensitive information or transferring funds. DMARC’s ability to reject unauthorized emails dramatically reduces the success rate of such campaigns, protecting both the organization and its customers from financial losses and data breaches. Industry data consistently shows that organizations with DMARC policies at enforcement levels experience a significantly lower incidence of email-based fraud.
Marketing Effectiveness and ROI: For marketing teams, deliverability is the lifeline of their campaigns. Unauthenticated emails are far more likely to land in spam folders or be blocked outright, rendering marketing efforts ineffective. This translates directly to lost leads, missed sales opportunities, and a diminished return on investment (ROI) for email marketing programs. By ensuring emails consistently reach the inbox, authentication directly contributes to higher open rates, click-through rates, and ultimately, conversions. The visual trust provided by BIMI further enhances this, making emails stand out and improving engagement.
Operational Efficiency and Compliance: Managing email deliverability without proper authentication can be a constant battle against spam filters and blacklists, consuming valuable IT and marketing resources. Proactive authentication reduces these operational headaches. Furthermore, compliance with evolving MBP mandates is becoming a fundamental aspect of maintaining access to the inbox, making authentication a critical component of any digital strategy.
Challenges and Best Practices for Senders
While the benefits are clear, implementing and maintaining robust email authentication can present challenges, especially for organizations with complex sending architectures or limited technical resources. The primary difficulties often revolve around:
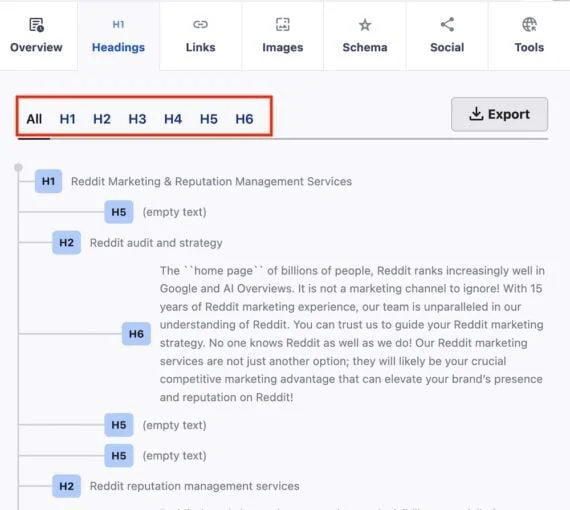
- Technical Complexity: Understanding DNS records, cryptographic keys, and DMARC syntax requires specific technical expertise.
- Third-Party Senders: Many organizations use multiple ESPs or marketing automation platforms. Each of these must be correctly configured for SPF and DKIM, and their domains must align with DMARC.
- Monitoring and Maintenance: DMARC reports need to be regularly parsed and analyzed to identify issues and unauthorized sending. SPF records require careful management to avoid the 10-lookup limit.
To overcome these challenges, organizations should adopt several best practices:
- Start with DMARC
p=none: Begin by deploying a DMARC record with ap=nonepolicy to gather data and understand your email sending ecosystem without impacting deliverability. - Utilize DMARC Reporting Tools: Leverage specialized tools to parse and visualize DMARC aggregate reports, making the data actionable.
- Audit All Sending Sources: Identify every service that sends email on behalf of your domain (ESPs, transactional email services, CRM platforms, internal mail servers) and ensure each is correctly authenticated.
- Gradual Policy Enforcement: Once comfortable with the data from
p=none, gradually move top=quarantineand eventuallyp=reject, monitoring closely at each stage. - Prioritize Key Lengths: Ensure all DKIM keys are at least 2048 bits long.
- Consider BIMI: Once DMARC is at enforcement, explore BIMI to add a visual trust signal to your emails.
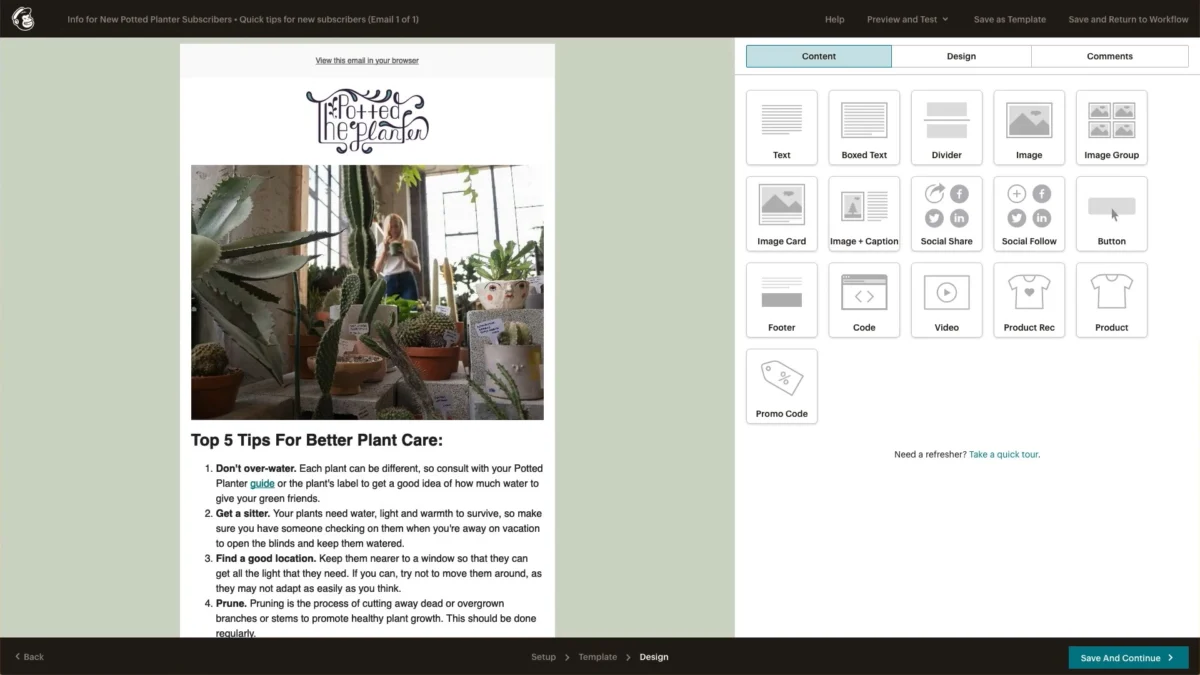
- Leverage Expertise: For organizations lacking in-house expertise, partnering with email deliverability consultants or utilizing platforms that provide infrastructure checks, such as Litmus, can be invaluable for ensuring all authentication measures are correctly configured and maintained.
The Road Ahead: Continuous Vigilance and Future Trends
Email authentication, while now a non-negotiable foundation, is not a static solution but rather an ongoing commitment to email security and trust. The landscape of cyber threats is constantly evolving, and so too will the mechanisms designed to combat them. Future trends may include deeper integration of AI and machine learning for real-time threat detection, even more stringent verification processes, and potentially new standards that further enhance sender identity and message integrity.
The stakes for email senders have never been higher. With the unified stance of Gmail, Yahoo, and Microsoft on authentication requirements for bulk senders, getting this right is no longer merely about optimizing deliverability; it is about preserving the fundamental trust relationship with subscribers and customers. Properly configuring SPF, DKIM, and DMARC is the essential starting point. Progressing to DMARC enforcement, diligently monitoring aggregate reports, and strategically implementing BIMI are all critical steps towards cultivating a more protected, trusted, and ultimately more effective email program. While this endeavor requires dedicated time and coordination across various departments, the payoff in terms of enhanced brand reputation, improved deliverability, and robust cybersecurity is undeniably worth the investment.