In an increasingly competitive digital landscape, where every marketing dollar is scrutinized for its return, the foundational practice of email verification has emerged as an indispensable prerequisite, not merely a routine maintenance task. While marketers meticulously craft compelling messages, optimize design, and deploy sophisticated A/B testing or AI-generated copy, these efforts are fundamentally undermined if the intended recipients cannot be reached. Without a robust email verification strategy, businesses risk making expensive mistakes, eroding sender reputation, and misallocating precious resources.
The Evolving Landscape of Email Marketing and Deliverability
The modern email marketing environment is a complex ecosystem, far removed from its early, less regulated days. The proliferation of unsolicited commercial email, or "spam," in the late 1990s and early 2000s necessitated the development of sophisticated filtering mechanisms by internet service providers (ISPs) and mailbox providers (MBPs) like Google, Microsoft, and Yahoo. These systems continuously analyze various signals to determine the legitimacy and desirability of incoming emails. Central to this process is "sender reputation," a score assigned to an email sender based on factors such as bounce rates, spam complaint rates, engagement metrics (opens, clicks), and whether their IP address or domain appears on blacklists. A poor sender reputation can lead to emails being shunted to spam folders, or worse, outright blocked, irrespective of the quality of the content.
This evolution has fundamentally shifted the focus for marketers from simply "sending emails" to "ensuring deliverability." The challenge is compounded by the natural decay of email lists, which can see 20-30% of addresses become invalid or inactive annually, particularly in fast-moving sectors like Business-to-Business (B2B). Employees change jobs, companies merge or dissolve, and domains expire, rendering previously valid contacts obsolete. Against this backdrop, proactive email verification becomes not just a best practice, but a critical component of risk management and strategic resource allocation.
The Imperative of Email Verification: A Deeper Dive into ‘Why’
Email verification is crucial because it directly addresses the core challenge of deliverability. An invalid or nonexistent email address acts as an "invisible ceiling" on a campaign’s return on investment (ROI). When emails are sent to these addresses, they result in "hard bounces." A hard bounce is a permanent delivery failure, indicating that the email address does not exist, the domain name is invalid, or there is a persistent server error. MBPs view high hard bounce rates as a strong indicator of poor data management practices and, consequently, a potential sign of spamming behavior.
Industry data consistently highlights the detrimental impact of high bounce rates. According to various studies, a bounce rate exceeding 2% can begin to negatively affect sender reputation, while rates above 5% are often considered alarming and can trigger aggressive filtering. The immediate consequence is that future legitimate emails are more likely to be classified as spam, even for genuine, engaged leads. In severe cases, MBPs may even temporarily or permanently block emails from a particular sender’s domain or IP address, effectively crippling an entire communication channel. Proactive verification mitigates this risk significantly, allowing businesses to scale their campaigns confidently without fear of suspension or deliverability roadblocks.
Beyond technical performance, verification protects the integrity of creative assets. Marketers invest substantial time and resources into crafting engaging copy, designing visually appealing templates, and implementing sophisticated personalization strategies. Without a clean, verified list, a significant portion of these efforts is wasted on non-existent recipients. By cleaning the email database, organizations establish a sound foundation of valid data, ensuring that their creative assets are leveraged to their fullest potential and seen by as many relevant leads as possible. This translates directly into more accurate analytics, better campaign optimization, and ultimately, improved ROI.
Unpacking the Downstream Fallacy: A Strategic Misstep

Many marketing teams fall prey to what can be termed the "downstream fallacy." This phenomenon occurs when organizations pour disproportionate resources into the latter stages of the marketing workflow – focusing on content creation, design, A/B testing, and automation – while neglecting the fundamental quality of their data at the initial stages. The pressure on marketers to demonstrate visible results, often measured by email output and engagement metrics, can inadvertently lead to this oversight. However, accurately analyzing the success of creative changes or personalization efforts becomes virtually impossible if the underlying email list is riddled with invalid addresses.
The advent of artificial intelligence (AI) and hyper-personalization in email marketing further amplifies this issue. While these innovative technologies promise unprecedented levels of engagement and relevance, their true potential cannot be realized if they are deployed against an unverified list. Sending a perfectly personalized, AI-generated email to an address that doesn’t exist is not only a waste of resources but also actively detrimental to sender reputation. The most advanced tools cannot compensate for a nonexistent recipient.
Furthermore, poor data quality often creates significant misalignment and friction between marketing and sales teams. When marketing passes on leads that include invalid email addresses, sales representatives waste valuable time attempting to contact "ghosts." This leads to frustration, reduced productivity, and an erosion of trust in the quality of leads generated by marketing, hindering overall business growth and departmental synergy.
Compounding these challenges are tighter marketing budgets. A 2025 Gartner report highlighted that marketing budgets have flatlined at 7.7 percent of overall company revenue, underscoring the critical need for efficiency and resource maximization. In an environment of constrained spending, sending emails to invalid domains or nonexistent contacts represents a direct financial drain. Correcting the downstream fallacy necessitates a fundamental shift in perspective: placing greater emphasis "upstream" on audience validity as the primary launchpad for all subsequent marketing activities. This ensures that every dollar spent on creative, technology, and personnel is directed towards genuinely reachable prospects.
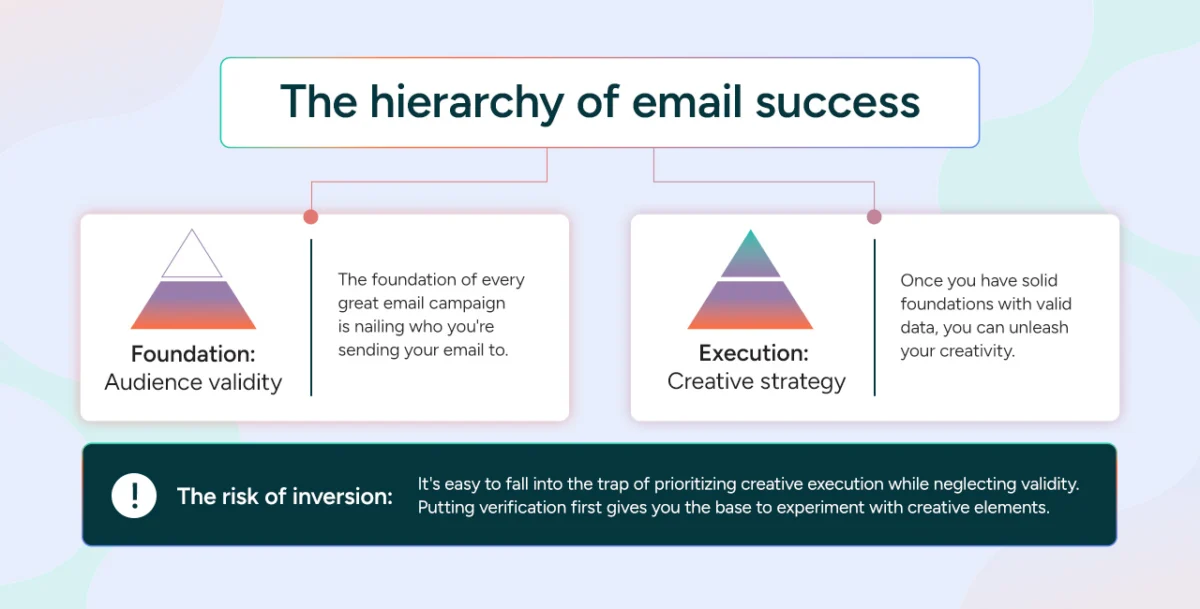
The Foundational Hierarchy of Email Success
A truly successful email campaign, while ultimately dependent on strong creative elements, must be built upon a logical and robust hierarchy of priorities. Inverting this hierarchy risks superficial success and underlying inefficiencies.
1. Foundation: Audience Validity
The absolute bedrock of any effective email campaign is a meticulously validated audience. This step involves more than just identifying valid email accounts; it encompasses understanding who the messages are being sent to. By ensuring the validity of email addresses at the outset, marketers prevent their efforts from becoming "shouting into the void." This foundational step directly informs the entire creative strategy and ensures that resources are deployed efficiently.
Implementing robust verification processes early on pays dividends in both the short and long term. It guarantees that the initial outreach is to a healthy, responsive list, and as campaigns scale, it prevents the accumulation of bad data that would inevitably lead to escalating bounce rates and damaged sender reputation. This proactive approach safeguards deliverability and fosters sustainable growth.
2. Execution: Creative Strategy
Only once a solid foundation of valid data is established can marketing teams truly unleash their creativity. This layer encompasses the art and science of compelling copy, engaging design, and intelligent personalization tactics. While the creative strategy is undeniably responsible for capturing attention, driving engagement, and prompting conversions, its effectiveness is entirely contingent upon the underlying deliverability achieved through email verification. A brilliant email that never reaches the inbox is, by definition, a failure.
3. The Risks of Inversion and the Call for a Cultural Shift
The ease with which marketers can prioritize creative execution over list hygiene presents a significant trap. Focusing on metrics like open rates and click-through rates (CTRs) without first ensuring audience validity can create a false sense of security. An impressive CTR on a small, delivered segment of a campaign might mask the fact that a large portion of the emails never reached their intended recipients due to invalid addresses. This inversion leads to misinformed optimization efforts, as data analysis is skewed by an unrepresentative sample.
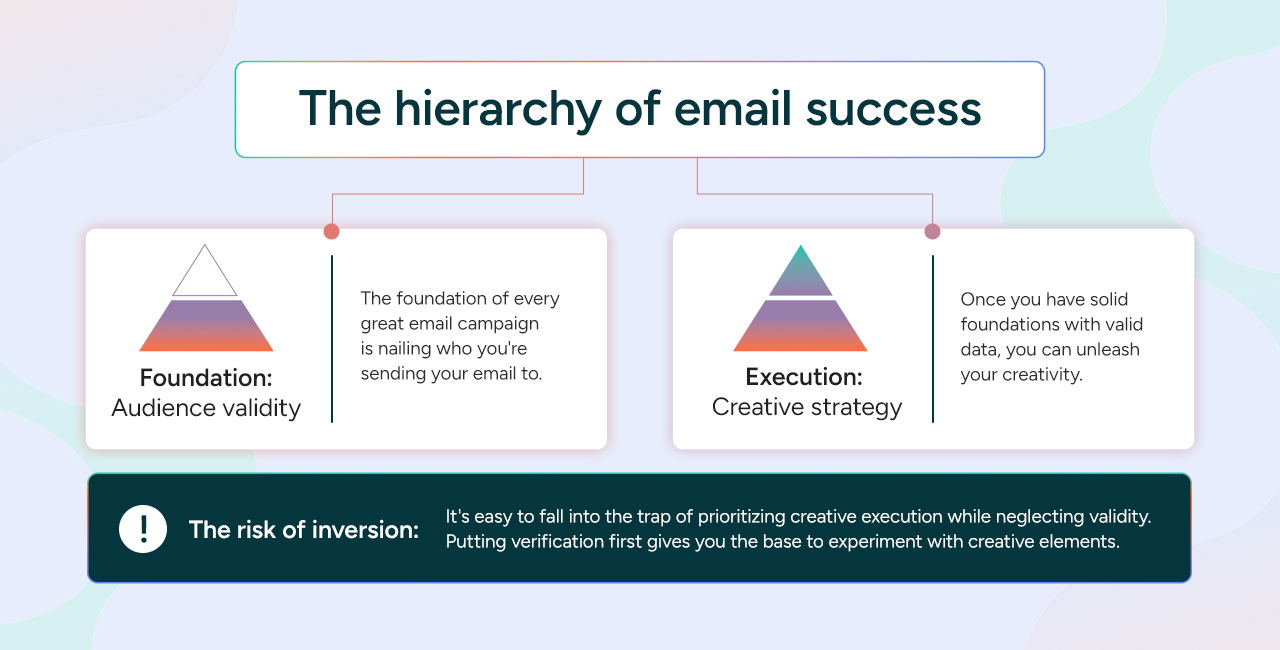
To rectify this strategic inversion, a profound cultural shift within marketing teams is essential. Organizations must begin to champion and reward metrics related to data cleanliness and audience validity with the same fervor as they do engagement metrics. Recognizing that a low bounce rate and a high deliverability rate are as crucial, if not more so, than a high click-through rate, is fundamental to building a sustainable and genuinely impactful email marketing program. This cultural change fosters a holistic view of campaign success, integrating data quality as an intrinsic part of overall performance.
The Mechanics of Verification: Beyond Simple Syntax
Email verification is a sophisticated process that extends far beyond a rudimentary check for an "@" symbol. A comprehensive verification tool employs a multi-layered technical process to ascertain the validity and deliverability of an email address.
Beyond Basic Syntax
Basic syntax checks are the first line of defense, ensuring an email address conforms to standard formatting (e.g., [email protected]). While these checks can quickly filter out obvious typos or malformed entries, they cannot determine if an address is actually active, if the inbox is full, or if the server is configured to reject external mail. True verification delves much deeper:
- DNS (Domain Name System) Checks: Verifies that the domain exists and is properly configured.
- MX (Mail Exchange) Record Checks: Confirms that the domain has valid mail exchange records, indicating it can receive emails.
- SMTP (Simple Mail Transfer Protocol) Connection: Attempts to establish a connection with the email server associated with the domain. This step simulates sending an email without actually delivering it, allowing the verification service to query the server about the existence of the specific user. This is a critical step for identifying nonexistent users.
- Temporary vs. Permanent Failures: Advanced tools distinguish between permanent failures (e.g., nonexistent users, invalid domains, spam traps) which warrant immediate removal, and temporary issues (e.g., full mailboxes, server timeouts, temporary blocks) which might resolve themselves and can be re-attempted under controlled conditions. This distinction is vital for maintaining sender reputation and recovering potentially valuable leads.
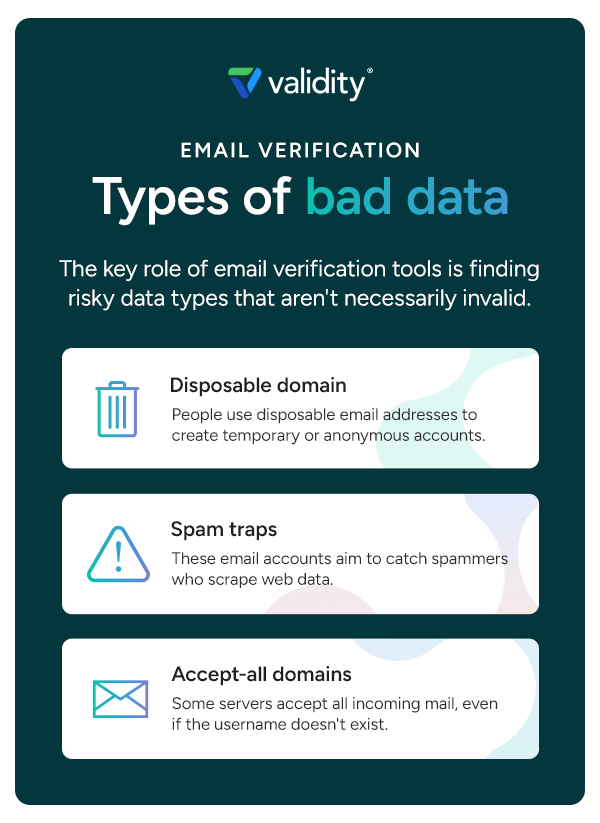
Types of Bad Data
Email verification tools are designed to identify various categories of "risky" or "bad" data, some of which are not technically invalid but still pose a threat to email programs:
- Non-existent Emails: These are the most common form of bad data, leading directly to hard bounces.
- Spam Traps: These are email addresses specifically designed to catch spammers. They can be pristine (never used for legitimate communication) or recycled (old, abandoned addresses reactivated as traps). Hitting a spam trap severely damages sender reputation and can lead to immediate blacklisting.
- Disposable Email Addresses (DEAs): Also known as "burner" emails, these are temporary addresses used to sign up for services without revealing a primary email. They often indicate low intent and high churn, making them undesirable for long-term engagement.
- Catch-all Domains: These domains are configured to accept all emails sent to them, regardless of whether the specific user mailbox exists. Verification tools can flag these as "unknown" because a direct user existence check isn’t possible, leaving marketers uncertain about deliverability.
- Role-based Emails: Addresses like
info@,sales@,support@are often shared by multiple people and can lead to lower engagement, higher spam complaints (if multiple people delete the email), or a perception of impersonal communication. - Blocked/Blacklisted Domains: Emails from domains known for abusive behavior or frequently appearing on blacklists.
- Syntax Errors: Simple formatting mistakes.
Beyond performance, identifying and removing these risky data types is crucial for regulatory compliance. By minimizing the risk of hitting spam traps or sending to purchased lists (which often contain high-risk domains and unconsented contacts), businesses significantly reduce their exposure to violations of data privacy regulations such as the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and Canada’s Anti-Spam Legislation (CASL). These regulations mandate consent and data accuracy, making verification an essential compliance tool.
The Real Cost of Bad Data: Protecting Your Bottom Line
Eliminating bad data from an email list is not merely about optimizing technical performance; it is a direct investment in protecting and enhancing a company’s financial health. The costs associated with poor data quality manifest in both direct and indirect forms, as well as significant opportunity costs.
Direct Costs
Email service providers (ESPs) typically charge based on the volume of emails sent or the number of active subscribers. By maintaining a list bloated with invalid or nonexistent contacts, businesses are directly paying for services they cannot effectively utilize. Purging these non-deliverable contacts immediately eliminates this waste, ensuring that budget allocations are focused solely on verifiable, reachable leads. Streamlining an email list can often result in bumping down to a lower pricing tier with an ESP, generating immediate and tangible cost savings. Furthermore, storing and processing large amounts of invalid data incurs unnecessary overhead in CRM systems and other marketing technology platforms, increasing storage and processing costs.
Indirect Costs
The ripple effects of bad data extend far beyond direct expenditures. One significant indirect cost is the skewing of analytics. When campaign performance metrics (open rates, click-through rates, conversion rates) are calculated against a list containing a substantial percentage of invalid addresses, the resulting data is inherently flawed. This leads to inaccurate conclusions about campaign effectiveness, misinformed A/B testing, and ultimately, suboptimal strategic decisions. With a verified list, marketers can report with confidence on the true impact of their efforts, enabling more effective optimization of future strategies.
Perhaps the most insidious indirect cost is the degradation of sender reputation. Every hard bounce signals to MBPs that the sender’s data hygiene is lacking. Over time, this cumulative negative feedback can lead to emails being consistently routed to spam folders, or even blocked. The cost here is not just lost reach for a single campaign, but a long-term impairment of the ability to communicate effectively with all leads, including genuine, engaged customers. Rebuilding a damaged sender reputation is a time-consuming and expensive endeavor, often requiring dedicated resources, IP warming, and a meticulous adherence to best practices for an extended period. Proactive verification effectively insulates against this costly repair work, allowing marketing teams to focus on growth rather than remediation.
Invalid data also creates operational drag within an organization. When marketing passes unverified leads to sales, sales teams waste valuable time pursuing contacts that are either nonexistent or unresponsive. This inefficiency translates into lost productivity, extended sales cycles, and a breakdown of trust between critical departments. Regularly verified data equips sales teams with genuinely actionable leads, enabling them to focus their efforts where they will have the greatest impact. Moreover, bloated databases with large amounts of bad data can slow down synchronization times between various platforms (CRM, marketing automation, ESP), increasing technical overhead and potentially raising storage costs for backups.
Opportunity Costs
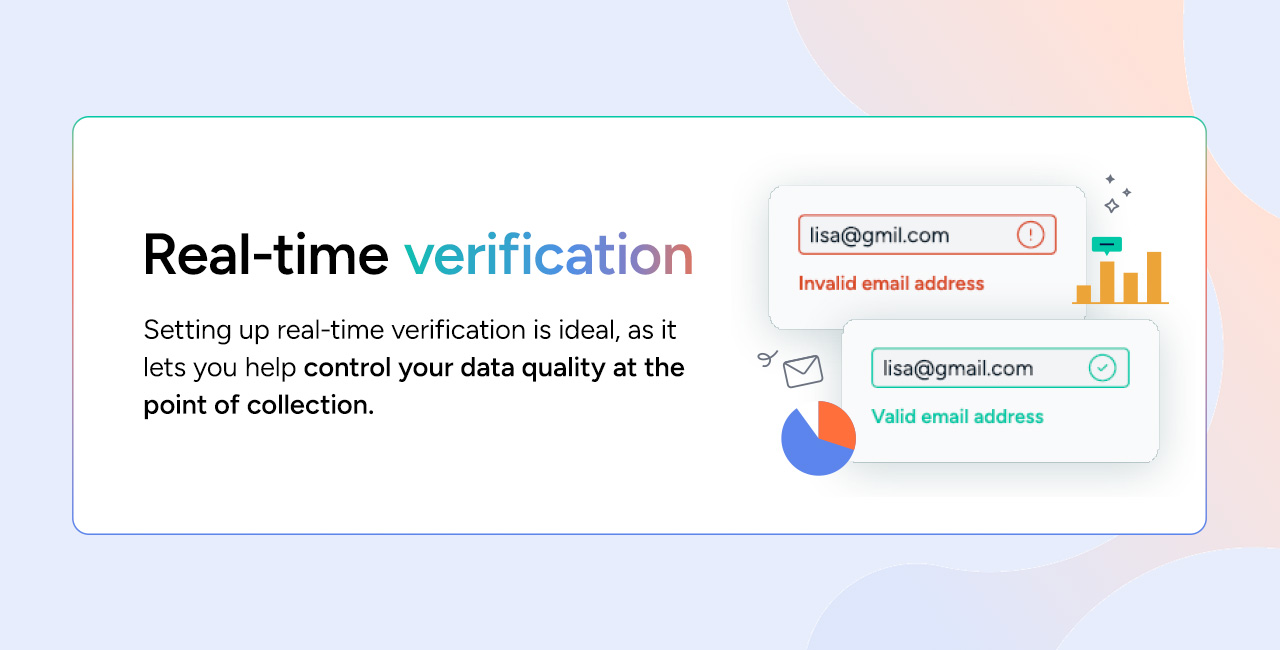
Beyond the measurable direct and indirect costs, there are significant opportunity costs associated with bad data. These include leads that could have been "saved" at the point of capture. For instance, a simple human typo in a domain name (e.g., gamil.com instead of gmail.com) can be instantly identified and corrected with real-time verification tools. Without such a mechanism, a potentially valuable prospect is lost, along with all the future engagement and revenue they might have generated. Real-time correction not only recovers these leads but also creates a frictionless user experience, reinforcing the brand’s professionalism and ensuring prospects receive the information they requested instantly. The opportunity cost is the sum of all potential conversions, customer lifetime value, and brand loyalty that are forfeited due to preventable data errors.
Implementing a Robust Verification Strategy: A Multi-faceted Approach
An effective email verification strategy is not a one-time fix but a continuous process integrated into the entire marketing workflow. It combines different types of verification to ensure data quality at every stage.
Real-time Verification
Implementing real-time verification at the point of data collection is the ultimate preventative measure. This involves integrating application programming interfaces (APIs) into web forms, sign-up pages, and checkout processes. When a user enters an email address, the API instantly checks its validity. If a typo is detected (e.g., yaho.com instead of yahoo.com), the system can prompt the user to correct it immediately. This not only prevents bad data from entering the customer relationship management (CRM) system but also enhances the user experience by providing instant feedback. For sales teams, this means they receive leads that are already validated, significantly reducing hand-off anxieties and improving their efficiency.
Bulk Verification
While real-time verification prevents new bad data, existing databases often require a thorough clean-up. Bulk verification tools allow organizations to upload large existing email lists for comprehensive validation. This is particularly crucial for legacy lists that may have accumulated invalid addresses over years. Data naturally decays; even a perfectly clean list from six months ago will have a percentage of invalid addresses today. This decay is especially pronounced in the B2B sector, where job changes, company closures, and domain expirations are frequent. Regular bulk verification, perhaps quarterly or semi-annually depending on list size and industry velocity, is essential to maintain data integrity and optimize existing assets.
Regular Maintenance
Beyond bulk clean-ups, integrating data hygiene as a regular part of the marketing maintenance schedule is paramount. This involves setting a consistent cadence for verifying and purging emails, catching invalid addresses before the next major send. The ideal cadence depends on the organization’s specific needs, the volume of new leads, and the industry. High-velocity industries like SaaS or e-commerce, where lead churn can be rapid, may require monthly or even bi-weekly verification. Regular maintenance helps to significantly reduce hard bounces, improve deliverability, and ensure that the "active audience" accurately reflects the "actual audience," leading to more reliable campaign performance metrics.
Verify Before Sending
For critical, high-stakes campaigns, such as Black Friday sales, product launches, or major seasonal promotions, a final verification pass immediately before sending is a non-negotiable best practice. These campaigns often carry significant revenue expectations, and ensuring the highest possible deliverability is paramount. An up-to-date, meticulously validated list maximizes the chances of these crucial emails reaching their intended recipients, boosting campaign success and safeguarding the sender’s reputation at critical junctures.
Manage the Unknowns
Even with the most advanced verification tools, a small percentage of email addresses may return an "unknown" status. This can be due to server timeouts, strict recipient security settings that prevent full SMTP verification, or other technical ambiguities. A common mistake is to treat these unknowns as valid and include them in subsequent campaigns, which can inadvertently increase bounce rates and harm sender reputation.
A more strategic approach involves segmenting these "unknown" contacts onto a separate "quarantine list." These contacts can then be tested with low-volume, text-only re-engagement emails. By using a secondary sending IP address for these tests, the primary sender’s reputation remains protected. If an email to an unknown address bounces, it can be permanently removed. If it goes through and shows engagement, the contact can be moved back to the main list. This methodical approach allows for the recovery of genuine leads while carefully managing potential risks.
Industry Leadership: Validity BriteVerify
When selecting an email verification partner, speed, accuracy, and integration capabilities are paramount. Validity’s BriteVerify solution has established itself as an industry standard, trusted by tens of thousands of organizations globally for its ability to significantly improve customer data quality.
BriteVerify is engineered to handle massive data volumes with minimal latency. Its real-time verification API integrates seamlessly into web forms and applications, ensuring that the user experience is never slowed down. Whether processing thousands of leads hourly or millions of records in a bulk batch, the tool scales effortlessly to meet diverse operational demands without compromising performance.
The accuracy of email verification hinges on the quality and breadth of the provider’s network. BriteVerify benefits from close relationships with major inbox providers and leverages a vast global data network. This deep integration allows for more precise and reliable status checks compared to competitors who may rely on less sophisticated data scraping methods. By reducing the number of "unknown" results in email lists, BriteVerify enables organizations to retain more genuinely valid leads while effectively identifying and removing bad data that could jeopardize sender reputation.
Furthermore, BriteVerify is designed for seamless integration into existing marketing and CRM systems, minimizing the headache and resource investment typically associated with onboarding new technologies. Its robust API and pre-built connectors facilitate rapid deployment, allowing businesses to quickly implement and benefit from enhanced data hygiene.
Maximize Every Send with BriteVerify
Prioritizing email verification is a strategic imperative that empowers marketing teams to optimize their resources, foster innovation, and drive measurable results. With trusted, clean data as a foundation, organizations can confidently invest in advanced personalization, AI-driven content, and sophisticated A/B testing, knowing that their efforts will reach their intended audience.
Validity BriteVerify provides the comprehensive tools necessary to achieve this foundational data quality. It enables verification at the critical point of capture, through regular bulk validations of existing databases, and even immediately before sending high-stakes campaigns. This multi-layered approach protects sender reputation, ensures optimal deliverability, and maximizes the engagement with genuinely interested leads.
To unlock the full potential of your email marketing efforts and transform data hygiene from a challenge into a competitive advantage, get started by requesting a demo today.