The rapid evolution of Large Language Models (LLMs) has transitioned from simple conversational interfaces to complex, agentic systems capable of interacting with external software environments. At the forefront of this shift is the Model Context Protocol (MCP), an open standard designed to provide a universal interface for AI models to connect with data sources and tools. However, as organizations move beyond experimental use cases, the challenges of security, governance, and workflow consistency have become paramount. By integrating MCP with n8n—a powerful low-code automation platform—and utilizing the Model Context Protocol Optimizer (MCPO), technical teams can now transform volatile AI interactions into structured, secure, and highly efficient enterprise workflows.

The Emergence of the Model Context Protocol in Enterprise Automation
The Model Context Protocol, introduced as an open standard to standardize how AI applications provide data and functionality to LLMs, solves a significant fragmentation problem in the AI ecosystem. Historically, connecting an AI model to a specific API required custom "glue code" that was often fragile and difficult to maintain. MCP provides a pre-defined architecture that allows models like Anthropic’s Claude or OpenAI’s GPT series to understand the capabilities of a connected service without manual configuration.
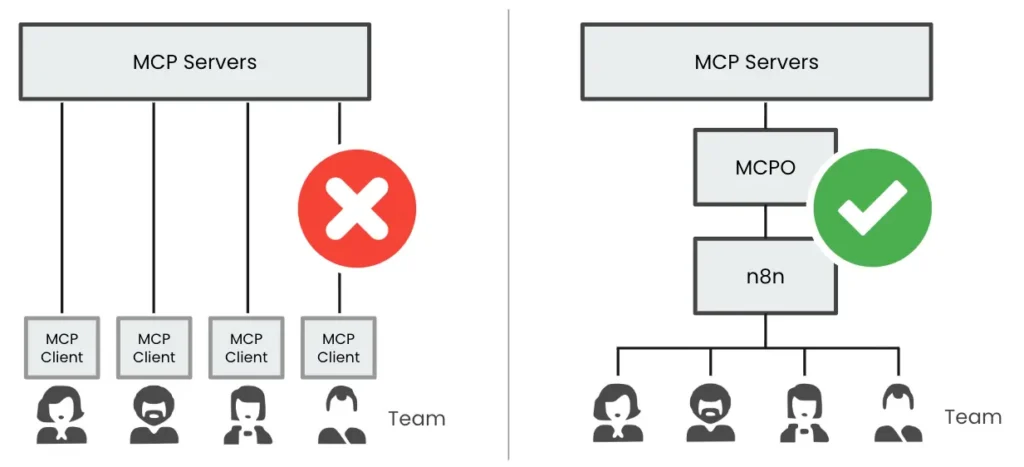
While MCP simplifies connectivity, it introduces a "black box" risk. When a model is granted direct access to an MCP server, it often possesses broad permissions to read, write, or execute commands. In a corporate environment, handing an LLM unrestricted tools can lead to inconsistent outputs, accidental data deletion, or security breaches. The solution lies in the orchestration of these protocols through a controlled intermediary. This is where the concept of MCPO (MCP Proxy) and n8n comes into play, providing a "human-in-the-loop" or "governed-by-design" framework that limits the AI’s scope to specific, pre-approved tasks.

The MCPO Architecture: Bridging the Gap Between AI and API
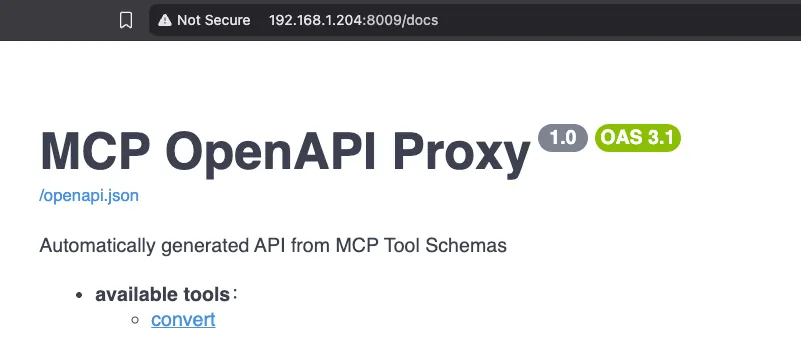
The primary frustration with traditional APIs is their complexity; they are powerful but often cumbersome to document and integrate for every new task. Conversely, MCPs are easy to use but difficult to control. The MCPO utility acts as a bridge, converting MCP services into well-documented API endpoints. This transformation allows developers to expose only the specific functionality required for a task, effectively applying the principle of "least privilege" to AI agents.
By deploying MCPO via Docker, organizations can centralize their MCP configurations. Instead of every team member managing individual MCP clients and local configurations, a single MCPO server can manage the connections to various tools—such as the Convert.com MCP server for A/B testing—and present them as a unified, secure API. This centralized approach ensures that API keys and secrets remain server-side, never exposed to the end-user or the raw LLM prompt.
Chronology of Implementation: From Raw Protocol to Structured Workflow
The transition from a raw MCP interaction to a production-ready n8n workflow follows a logical progression of five distinct phases.
Phase 1: Environment Virtualization and Configuration
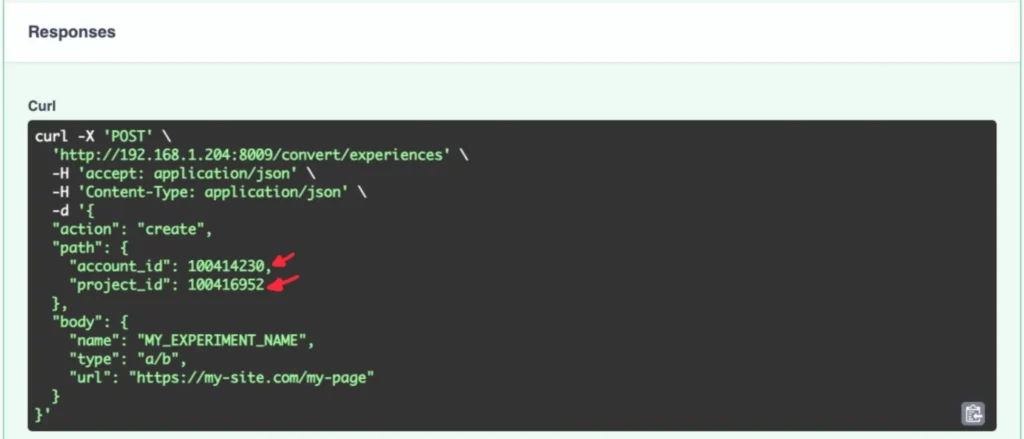
The process begins with the deployment of the MCPO service using Docker Compose. This environment ensures that the application is isolated and reproducible. The configuration involves a config.json file that defines the MCP servers the system will access. For instance, connecting to an experimentation platform requires defining the command (e.g., npx), the arguments for the specific MCP server package, and the necessary environment variables like API keys and secrets.
Phase 2: Discovery and Prototyping with Claude Code
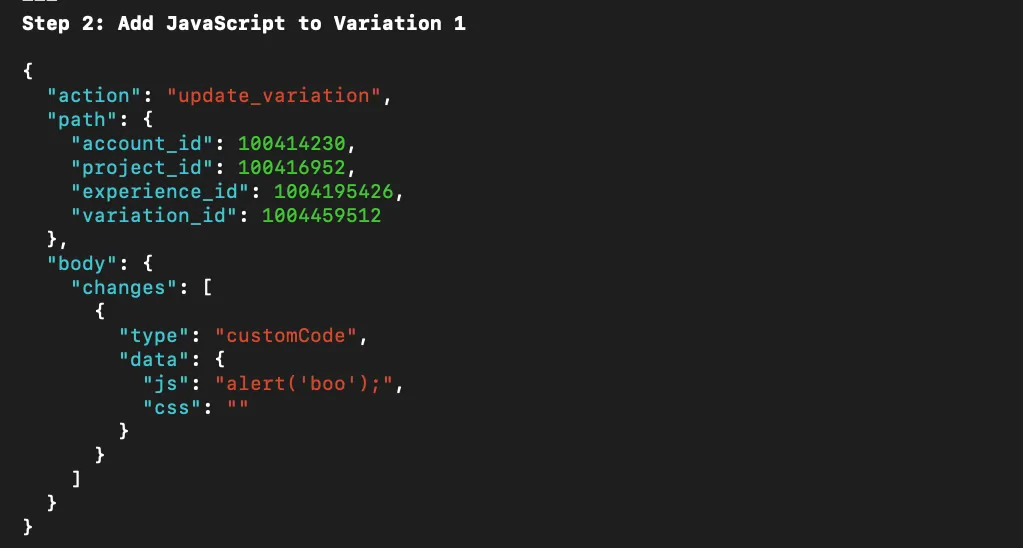
Before hard-coding a workflow, developers use tools like Claude Code to "learn" the optimal path of interaction. By interacting with the MCP server in a sandbox environment, the developer can identify which API calls are necessary to achieve a specific result, such as creating a new experiment or uploading a JavaScript variation. This stage acts as the "intelligence gathering" phase, where the raw JSON structures for API requests are identified and validated.
Phase 3: Building the n8n Orchestration Layer
With the necessary API calls identified, the developer moves to n8n to build the visual workflow. This layer handles the "pre-processing" of data. For an A/B testing use case, this includes:
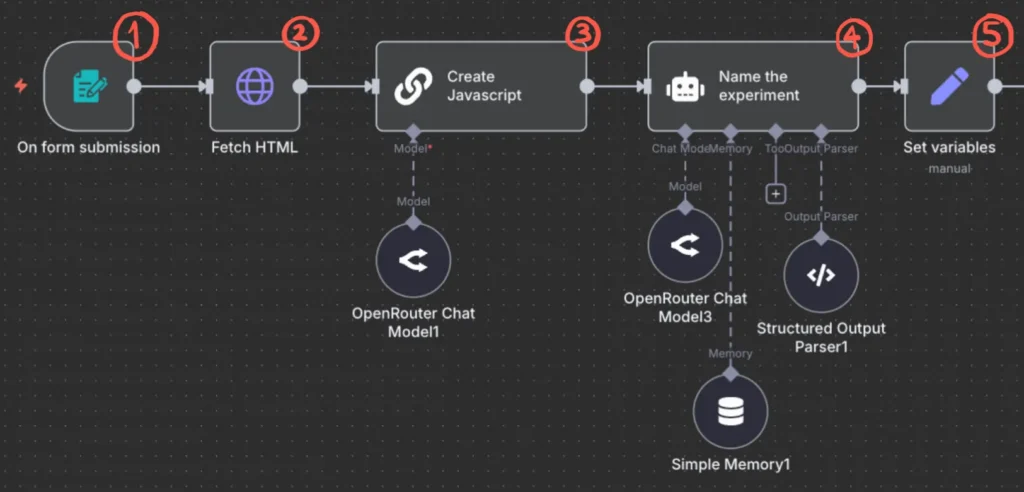
- Input Trigger: A form or webhook to collect the test requirements.
- Data Retrieval: Fetching the HTML of the target URL to provide context to the LLM.
- Refinement: Using a "Small Model" (a cost-efficient LLM) to generate the specific JavaScript required for the test based on the HTML provided.
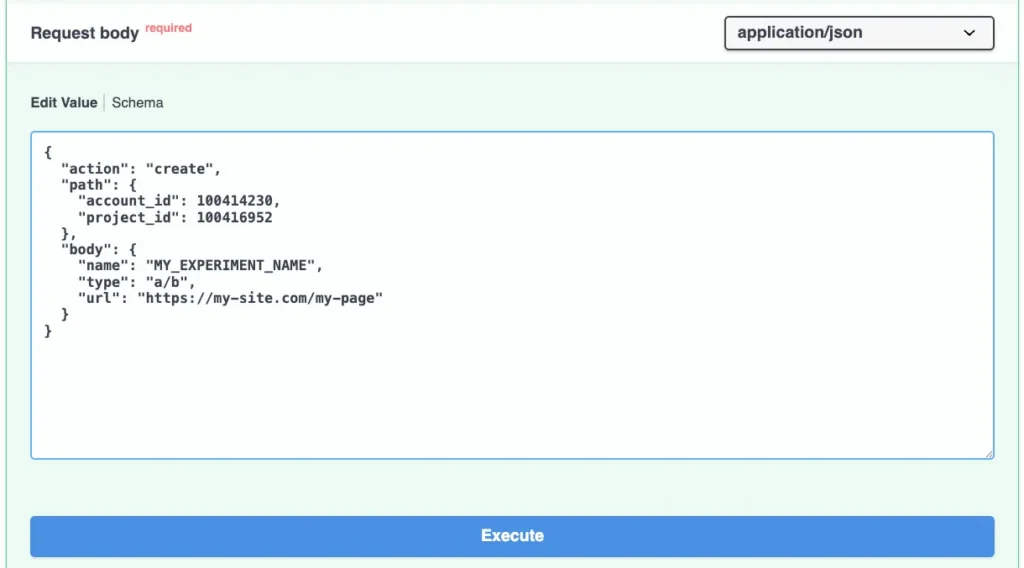
Phase 4: API Integration and Testing via Swagger
MCPO provides a Swagger-based UI, which allows for the testing of endpoints in real-time. The developer takes the JSON structures discovered in Phase 2 and tests them against the MCPO endpoints. Once validated, these are converted into HTTP Request nodes within n8n.
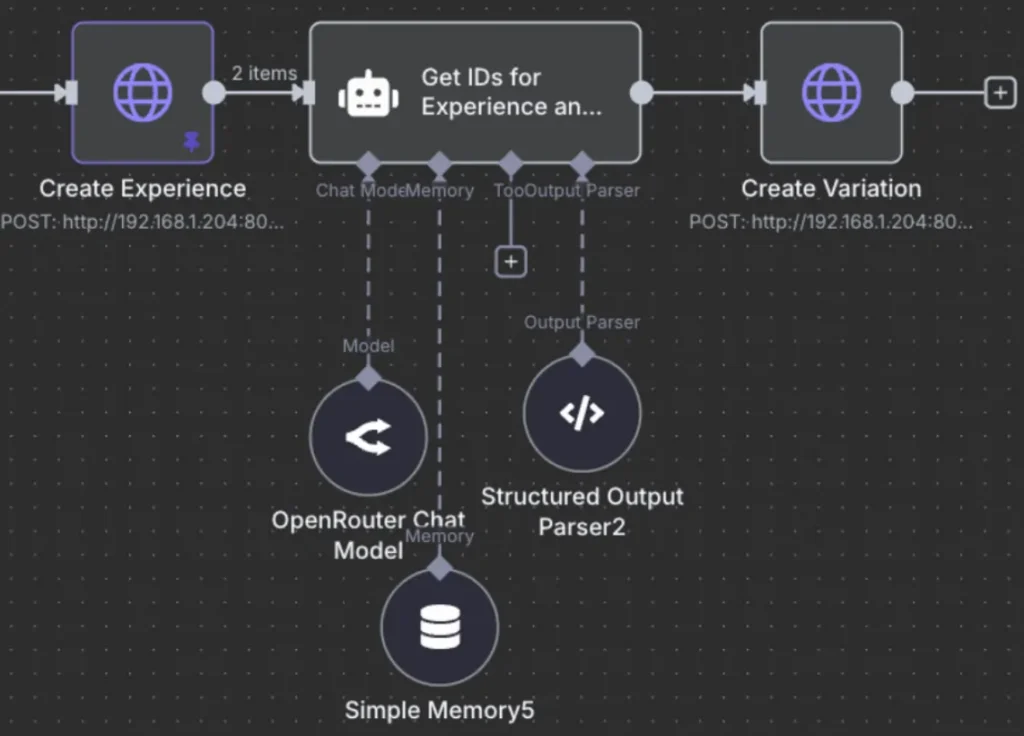
Phase 5: Governance and Variable Mapping
The final phase involves mapping dynamic data (like experiment IDs and variation codes) into the workflow nodes. By using n8n’s "Set" nodes, developers can bundle all necessary variables into a single object, ensuring that subsequent steps in the workflow have access to the correct context without redundant processing.
Technical Deep Dive: The Logic of the A/B Testing Workflow
The practical application of this system is best illustrated through the automated generation of A/B tests. In a traditional setup, a front-end developer would manually inspect a webpage, write a JavaScript variation, log into an experimentation platform, and manually create the test. This process is prone to human error and naming inconsistencies.
In the n8n-governed MCP workflow, the process is transformed into a five-step automated sequence. First, a form submission captures the user’s intent. Second, the system automatically fetches the live HTML of the site, ensuring the AI is working with the most recent code. Third, an AI agent—optimized through specific system prompts—generates the variation code. Fourth, the system generates a standardized experiment name based on pre-defined conventions. Finally, the MCPO-exposed API calls create the experiment and upload the code in one seamless operation.
Supporting data suggests that this structured approach can reduce the "time-to-launch" for simple front-end experiments by as much as 80%. By removing the manual "UI-clicking" phase of experiment setup, teams can focus on the strategic hypothesis rather than the technical implementation.
Security Implications and Official Responses
Industry analysts have noted that the "Agentic Workflow" trend is only viable if security keeps pace with capability. Direct MCP access is increasingly viewed as a high-risk configuration for enterprise environments. The use of an intermediary like n8n and MCPO aligns with the "Security by Design" framework promoted by major cybersecurity agencies.
While there have been no official "statements" in the traditional sense from regulatory bodies on MCP specifically, the general consensus among CTOs at leading SaaS companies is that abstraction layers are necessary. "The goal is to provide the AI with a ‘sandbox’ where it can be productive without being destructive," says one industry consultant specializing in AI automation. By turning MCP into a standard API, organizations can apply traditional web application firewalls (WAFs), rate limiting, and audit logging to AI actions—capabilities that are often missing in direct-to-model tool usage.
Broader Impact and the Future of Small Model Series
The integration of MCP into n8n workflows represents a significant milestone in the democratization of AI. It allows non-developers to trigger complex, multi-step technical processes through simple interfaces, while giving developers the tools to ensure those processes are safe and scalable.
Furthermore, this approach emphasizes the utility of "Small Models." Rather than using a massive, expensive LLM for every task, a structured n8n workflow can utilize smaller, specialized models for specific steps—such as naming an experiment or extracting an ID from a JSON response. This leads to a significant reduction in operational costs and latency.
As organizations continue to grapple with how to integrate AI into their core operations, the combination of MCP, MCPO, and n8n provides a blueprint for the future. It moves the conversation away from what AI can do in a vacuum and toward how AI can be integrated into the existing fabric of enterprise software. The result is a system that is not only more powerful than the sum of its parts but also more resilient, secure, and aligned with the rigorous demands of professional experimentation and development teams. By standardizing these workflows, companies can ensure that every team member, regardless of their technical proficiency, can leverage the full power of AI within a safe and optimized framework.